Computer based security and monitoring system for forensic experts
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Security Systems2.2 Evolution of Forensic Technology
2.3 Importance of Monitoring Systems
2.4 Role of Computers in Forensic Investigations
2.5 Digital Evidence Collection and Analysis
2.6 Use of Biometric Data in Forensic Science
2.7 Cybersecurity Measures for Forensic Experts
2.8 Data Encryption and Privacy Concerns
2.9 Case Studies in Forensic Technology
2.10 Emerging Trends in Forensic Investigations
Chapter THREE
3.1 Research Design and Methodology3.2 Selection of Data Collection Methods
3.3 Sampling Techniques
3.4 Data Analysis Procedures
3.5 Ethical Considerations
3.6 Research Limitations
3.7 Data Validation Techniques
3.8 Reliability and Validity
Chapter FOUR
4.1 Data Analysis and Interpretation4.2 Forensic Technology Adoption Rates
4.3 Impact of Security Systems on Investigations
4.4 Challenges Faced by Forensic Experts
4.5 Comparison of Monitoring Tools
4.6 Recommendations for Improvement
4.7 Future Directions for Research
4.8 Implications for Forensic Practice
Chapter FIVE
5.1 Summary of Findings5.2 Conclusion
5.3 Contributions to the Field
5.4 Practical Applications of Research
5.5 Recommendations for Further Study
Thesis Abstract
AbstractForensic investigations play a crucial role in solving crimes and providing evidence for legal proceedings. In today's digital age, the use of computer-based security and monitoring systems has become essential for forensic experts to efficiently gather, analyze, and present digital evidence. This research project focuses on developing an advanced computer-based security and monitoring system tailored to the needs of forensic experts. The proposed system will incorporate state-of-the-art technologies such as machine learning algorithms, data encryption techniques, and real-time monitoring capabilities to enhance the efficiency and accuracy of forensic investigations. By utilizing machine learning algorithms, the system will be able to analyze large volumes of digital data quickly and identify patterns that may be crucial to solving a case. Data encryption techniques will ensure the security and integrity of digital evidence, protecting it from unauthorized access or tampering. Real-time monitoring capabilities will enable forensic experts to track and analyze digital activities as they occur, allowing for the immediate identification of suspicious behavior or potential security threats. This proactive approach to monitoring will help investigators prevent cybercrimes and mitigate risks before they escalate. The system will also include features such as centralized data storage, case management tools, and customizable reporting functionalities to streamline the forensic investigation process. Centralized data storage will ensure that all digital evidence is securely stored and easily accessible to authorized personnel. Case management tools will help forensic experts organize and track the progress of investigations, improving collaboration and communication within investigative teams. Customizable reporting functionalities will allow users to generate detailed reports and presentations for legal purposes. Overall, the computer-based security and monitoring system developed in this research project will provide forensic experts with a powerful tool to enhance their capabilities in conducting digital investigations. By leveraging advanced technologies and innovative features, the system will enable investigators to efficiently gather and analyze digital evidence, ultimately leading to more successful outcomes in solving crimes and supporting legal proceedings.
Thesis Overview
INTRODUCTION
1.1 BACKGROUND OF THE STUDY
The world is becoming a smaller place in which to live and work. A technological revolution in communications and information exchange has taken place within business, industry and homes. Most developed and developing countries are substantially more invested in information processing
and Management than manufacturing goods, and this has affected their professional and personal lives. We bank and transfer money electronically and we are much more likely to receive an E-mail than a letter. It is estimated that the worldwide internet population is 349 million (Commerce Net Research Council 2000).
In this information technology age, some traditional crimes especially those concerning finance and commerce, continue to be upgraded technologically. Crimes associated with theft and manipulations of data are detected daily. Crimes of violence also are not immune to the effects of the information age. A serious and costly terrorist act could come from the internet instead of a truck bomb. The diary of a serial killer may be recorded on a floppy disk or hard disk drive rather than on paper in a notebook. Just as the workforce has gradually converted from manufacturing goods to processing information, criminal activity has to large extent also converted from physical dimension.
There calls a need for computer forensic experts and computer based monitoring and security system for easy capture of evidence of intruder who compromises a network or computer. This project dealt with the design and implementation of a computer based security and monitoring system for forensic experts, an ideal way for tracking the activities of an account user and also for recovering digital evidence of crime committed in a computer system.
STATEMENT OF THE PROBLEM
With the evolution of computer and the internet which has made the world a global village, so has criminals also taken advantage of this technological advancement to engage in different forms of cyber crime ranging from terrorism, internet fraud to the release of sophisticated viruses which is difficult to trace the perpetrators due to lack of sophisticated software that can retrieve information of such activities. This led to the design of a computer based security and monitoring system for forensic experts which will help in tracking the activities of internet users and for recovery of digital evidence of crime committed in a computer system.
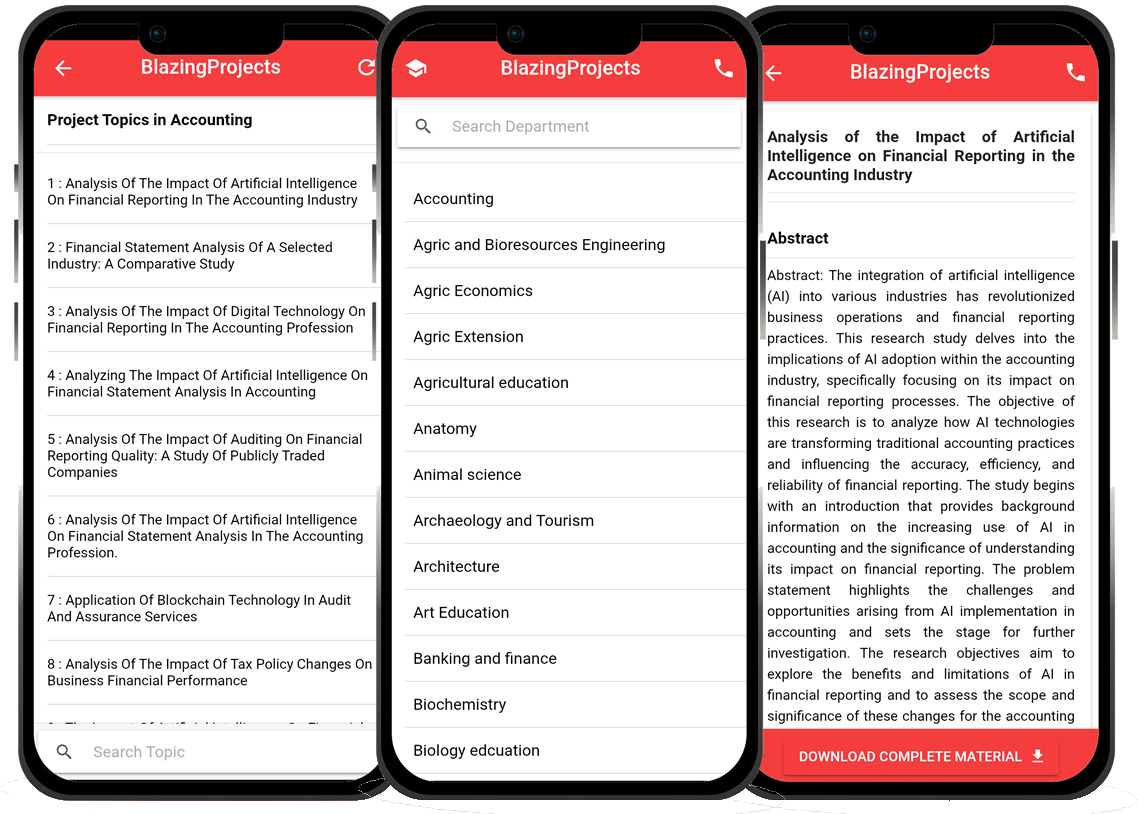
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Applying Machine Learning Techniques to Detect Financial Fraud in Online Transaction...
The project titled "Applying Machine Learning Techniques to Detect Financial Fraud in Online Transactions" aims to address the critical issue of detec...
Anomaly Detection in IoT Networks Using Machine Learning Algorithms...
The project titled "Anomaly Detection in IoT Networks Using Machine Learning Algorithms" focuses on addressing the critical challenge of detecting ano...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project titled "Applying Machine Learning Algorithms for Predicting Stock Market Trends" aims to explore the application of machine learning algor...
Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data...
The project titled "Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data" focuses on utilizing machine learning algorithms...
Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project titled "Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems" focuses on leveraging machine learning techniques ...
Implementation of a Machine Learning Algorithm for Predicting Stock Prices...
The project, "Implementation of a Machine Learning Algorithm for Predicting Stock Prices," aims to leverage the power of machine learning techniques t...
Development of an Intelligent Traffic Management System using Machine Learning Algor...
The project titled "Development of an Intelligent Traffic Management System using Machine Learning Algorithms" aims to revolutionize the traditional t...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
No response received....
Applying Machine Learning for Intrusion Detection in IoT Networks...
The project titled "Applying Machine Learning for Intrusion Detection in IoT Networks" aims to address the increasing cybersecurity threats targeting ...