Design and implementation of network-based security information system
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of study
1.3 Problem Statement
1.4 Objective of study
1.5 Limitation of study
1.6 Scope of study
1.7 Significance of study
1.8 Structure of the research
1.9 Definition of terms
Chapter TWO
2.1 Overview of Network-Based Security Information Systems2.2 Evolution of Network Security
2.3 Importance of Network Security
2.4 Types of Network-Based Security Systems
2.5 Network Security Protocols
2.6 Network Security Threats and Vulnerabilities
2.7 Network Security Best Practices
2.8 Network Security Technologies
2.9 Network Security Policies and Compliance
2.10 Case Studies in Network Security
Chapter THREE
3.1 Research Methodology Overview3.2 Research Design
3.3 Data Collection Methods
3.4 Sampling Techniques
3.5 Data Analysis Methods
3.6 Ethical Considerations
3.7 Research Limitations
3.8 Data Validity and Reliability
Chapter FOUR
4.1 Data Analysis and Interpretation4.2 Findings on Network-Based Security Information Systems
4.3 Comparison of Security Systems
4.4 Evaluation of Security Measures
4.5 Impact of Security Breaches
4.6 Recommendations for Enhanced Security
4.7 Future Trends in Network Security
4.8 Implications for Network Security Management
Chapter FIVE
5.1 Conclusion and Summary5.2 Summary of Findings
5.3 Contributions to Knowledge
5.4 Practical Implications
5.5 Suggestions for Future Research
Thesis Abstract
AbstractThe design and implementation of a network-based security information system is a critical aspect of modern cybersecurity measures. This research project focuses on developing a comprehensive system that can effectively monitor, analyze, and respond to security threats in a networked environment. The system incorporates advanced technologies such as intrusion detection systems, firewalls, and data encryption to enhance the security posture of organizations. The key components of the system include real-time monitoring of network traffic, anomaly detection, incident response mechanisms, and reporting tools. By integrating these components, organizations can proactively identify and mitigate security threats before they escalate into serious incidents. The system also includes a centralized dashboard that provides administrators with a holistic view of the network security status, enabling them to make informed decisions and take appropriate actions. The implementation of the system involves the deployment of sensors and agents across the network to collect and analyze security-related data. These sensors generate alerts when suspicious activities are detected, triggering automated responses or notifying security personnel for further investigation. The system is designed to be scalable and flexible, allowing organizations to adapt to evolving security threats and business requirements. The security information system employs machine learning algorithms to improve threat detection capabilities and reduce false positives. By continuously analyzing patterns in network traffic and user behavior, the system can identify potential security incidents with high accuracy. Moreover, the system leverages threat intelligence feeds and vulnerability databases to stay updated on the latest threats and security vulnerabilities. One of the key advantages of the network-based security information system is its ability to provide real-time visibility into network activities and security events. This enables organizations to respond promptly to security incidents and prevent data breaches or unauthorized access. The system also supports compliance requirements by generating audit logs and reports for regulatory purposes. Overall, the design and implementation of a network-based security information system are essential for organizations to protect their sensitive data and intellectual property from cyber threats. By leveraging advanced technologies and best practices in cybersecurity, organizations can enhance their overall security posture and reduce the risk of security breaches. This research project aims to provide a practical framework for designing and implementing an effective security information system that aligns with industry standards and regulatory requirements.
Thesis Overview
INTRODUCTION
Law enforcement administrations, Justice systems, legislators and the government functuraries often need information to efficiently disseminate and fulfill their official responsibilities of ensuring maximum security for their subjects. To achieve this, a system of information technology network is needed to aid the management in decision taking about the security of lives and properties. In this work “DESIGN AND IMPLEMENTATION OF A NETWORK BASED SECURITY INFORMATION SYSTEM” O will take a case study of “B’OPS COMMUNICATION OF POLICE SHQ ENUGU” as an existing information network system in the police and analyze their process of data collection and hence design a new system which will enhance the output.
1.1 OBJECTIVE OF THE STUDY
The objective of this program is strictly for the production of a reliable system of nationwide crime statistical information from all nooks and craings for administrative and operational use of the executive and law enforcement management system. Another objective of this work is to make an improvement in the existing data security system. To create a way of speedy data collections for security analysis. For a network of information technology for security purpose and create a standard management information system forecasting for security together with good decision taking, planning and control programs.
1.2 JUSTIFICATION
The process of executing the task of information management has been manually executed, quite unfortunately, the manual procedure reduces the output quality and consume time.
This work will examine a new system where the much needed human efforts are replaced with machines to achieve fast collection of data and easy processing to obtain healthy outputs.
Also the need for information and data in the knowledge base does not only answer to the problem of information over load but also helps in a state of crime statistics request, therefore the computerization of some of this areas is very necessary because its importance in making crime investigators imbibe new and modernized methods and create public awareness of the society security policy.
CHAPTER TWO
LITERATURE REVIEW
2.0 SECURITY CONCEPT
Security is defined in many ways due to the many contexts of its existence. In otherwords, security generally has to do with protection. It might be protection from undue access. Some attributes security to safe guiding from that which may or may not lead to destruction. It might also be interesting to understand that security has to do with protection of the environment. It also has to do with valuables, this means that anything has to be secured must have value. Things of less importance to humanity and therefore anything that pose threat to life must also be prevented. Security is a very important issue in any organization (system), no wonder VINCENT.E.ASOR in his seminar presentation at the Nigerian computer society’s conference of 2002 stated that an organization with 98 percent security is actually 100 percent insecure. This means that adequate security must be in place for a smooth running of an organizational affair or a system. The police which is the case study organsiation here defined security in the police training manual as the protection of lives and property coupled with the maintainance of law and order in a society.
2.1 SECURITY THREATS
They are criminal acts which have a particular harmful effects on peoples lives and property and do more than interfere with merely private rights. They are simply crimes. Now the above brings us to the crime concept. What is crime? According to the BLACKSTONE, crime is violation of public rights and duties due to the whole community considered as a community. Williams defined crime as acts that is capable of being followed by a criminal proceedings having one of the types of outcome – punishments.
Also Hulsbury’s law (adopted by the House of Lord’s in Board of Trade V. Owen 1957 as correct) defined crime as an unlawful act or default which is an offence against the public and render the person quilty of the act liable to legal punishment.
The summary of the above crime definitions by the police manual defined crime as an unlawful act committed by a person or a group of persons.
CHARACTERISTICS OF SECURITY THREATS
They are wrong doings which Judges have held, or the parliament has from time to time laid down which are sufficiently injurious to the public to warrant the application of a criminal procedure to deal with them, of course this does not enable us to recognize an act as a crime when we see one. Some acts are obviously harmful to the public that anyone would say they should be criminal and such acts almost certainly are, but there are many others about which opinions may differ widely. According to SIR CARLETON ALLEN, crime is crime because it consists of wrongdoings which directly and in serios degree threatens the security or well being of the society. This explains why acts have to be made crimes either by Judicial decisions or by legislation. A crime may remain a crime long after it has ceased to be a threat to the security or well-being of the society. THUS ALLEN’S proposition tells us what (as he thinks) ought to be crime rather than what is crime. The public nature of crimes is evidenced by the contrast between the rulers of civil and criminal procedure. Any citizen can, as a general rule and in the absence of some provision to the contrary bring a criminal prosecution, whether or not he has suffered any special harm over and above other members of the public. As a member of the public he has an interest in the enforcement of the criminal law.
CLASSIFICATION OF CRIMES
There is a problem that exist in the crime reporting system in Nigeria and especially the B’Ops comminication of the police, Enugu State branch in particular. This arises in the variations in definition of crimes among localities. This obstacle, as far as uniformity in definitions is concerned was removed by the adoption of a standard set ofcrime classification. To some extent the title of each classification generally commotes its content. However in reading the explanation of each category, it is very important to keep in mind that because of the differences between the state codes, there is no possibility in a system such as ‘felong’ and ‘misdemeamour’.
Crime classifications are in three categories. Viz crime against persons, crimes against property and crime of violence or crime against local acts.
Crime against persons include:
– Murder and non negligent manslaughter
– Aggravates assault
– Forcible rape
– Robbery
Crime against property includes:-
– Burglary
– Arson
– Stealing
– Forgery and counterfeiting
– Vandalism
Crimes against local acts include:
– Nacortic
– Illegal possession, carrying of weapons
– Prostitution and commercialized vice.
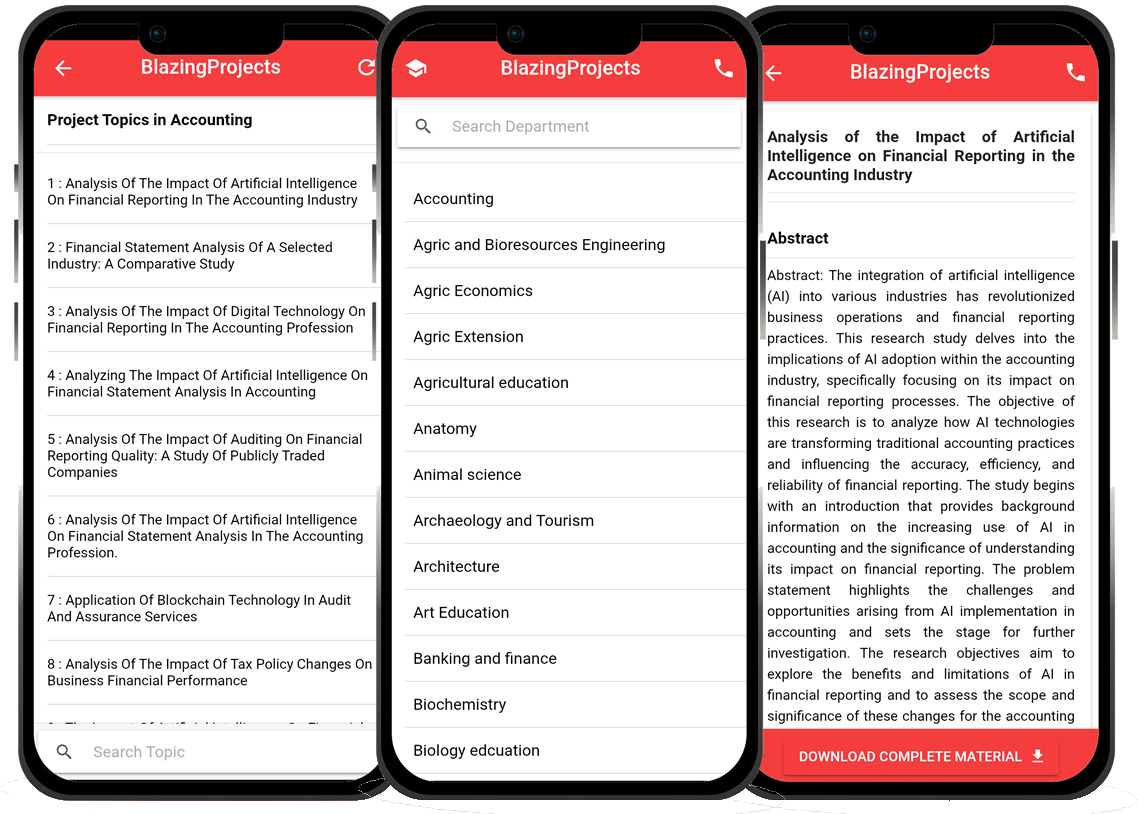
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Applying Machine Learning Techniques to Detect Financial Fraud in Online Transaction...
The project titled "Applying Machine Learning Techniques to Detect Financial Fraud in Online Transactions" aims to address the critical issue of detec...
Anomaly Detection in IoT Networks Using Machine Learning Algorithms...
The project titled "Anomaly Detection in IoT Networks Using Machine Learning Algorithms" focuses on addressing the critical challenge of detecting ano...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project titled "Applying Machine Learning Algorithms for Predicting Stock Market Trends" aims to explore the application of machine learning algor...
Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data...
The project titled "Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data" focuses on utilizing machine learning algorithms...
Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project titled "Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems" focuses on leveraging machine learning techniques ...
Implementation of a Machine Learning Algorithm for Predicting Stock Prices...
The project, "Implementation of a Machine Learning Algorithm for Predicting Stock Prices," aims to leverage the power of machine learning techniques t...
Development of an Intelligent Traffic Management System using Machine Learning Algor...
The project titled "Development of an Intelligent Traffic Management System using Machine Learning Algorithms" aims to revolutionize the traditional t...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
No response received....
Applying Machine Learning for Intrusion Detection in IoT Networks...
The project titled "Applying Machine Learning for Intrusion Detection in IoT Networks" aims to address the increasing cybersecurity threats targeting ...