The development of a state security database model
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Theoretical Framework2.2 Historical Overview
2.3 Conceptual Framework
2.4 Empirical Studies
2.5 Comparative Analysis
2.6 Current Trends
2.7 Key Concepts
2.8 Methodological Approaches
2.9 Technological Advancements
2.10 Future Directions
Chapter THREE
3.1 Research Design3.2 Population and Sampling
3.3 Data Collection Methods
3.4 Data Analysis Techniques
3.5 Research Instruments
3.6 Ethical Considerations
3.7 Validity and Reliability
3.8 Limitations of Methodology
Chapter FOUR
4.1 Overview of Findings4.2 Data Analysis Results
4.3 Interpretation of Results
4.4 Comparison with Literature
4.5 Implications of Findings
4.6 Recommendations
4.7 Future Research Directions
4.8 Conclusion of Findings
Chapter FIVE
5.1 Summary of Findings5.2 Conclusion
5.3 Implications for Practice
5.4 Contributions to Knowledge
5.5 Recommendations for Action
5.6 Reflections on the Research Process
5.7 Areas for Future Research
Thesis Abstract
AbstractThe development of a state security database model is a crucial aspect of modern security infrastructure. This research project aims to design and implement a comprehensive database model that can effectively store, manage, and analyze security-related data for a state or government entity. The model will incorporate various data sources, including law enforcement records, intelligence reports, surveillance data, and border control information. Key components of the database model will include a robust data schema that can accommodate diverse types of security data, data encryption mechanisms to ensure the confidentiality and integrity of sensitive information, and data access controls to restrict unauthorized access to the database. The model will also feature data analytics capabilities, allowing security personnel to identify patterns, trends, and potential security threats from the stored data. The research will involve a thorough analysis of existing security database models and best practices in data management and security. The design phase will focus on developing a flexible and scalable database architecture that can adapt to the evolving security needs of the state. Implementation will involve the creation of database tables, indexes, and queries to support efficient data storage and retrieval. In addition to the technical aspects of database development, the research will also address legal and ethical considerations related to the collection and use of security data. Compliance with privacy regulations, data protection laws, and information security standards will be a key priority in the design and implementation of the state security database model. The evaluation of the database model will involve testing its performance, scalability, and security features using simulated security scenarios and real-world data samples. User feedback and usability testing will also be conducted to assess the effectiveness of the model in supporting security operations and decision-making. Overall, the development of a state security database model is essential for enhancing the ability of state authorities to monitor, analyze, and respond to security threats effectively. By leveraging the power of data-driven insights, the model will empower security agencies to proactively address security challenges and safeguard the interests of the state and its citizens.
Thesis Overview
GENERAL INTRODUCTION
According to Gupta (2012), in a very short span of time, computer has grown from a scientific curiosity to an indispensable tool of modem society. There is hardly any scientific/technical or business activity which is not in one way or the other, affected by modern data processing techniques. The human mind can handle only a limited number of things at a time. The digital computer, on the other hand, can be programmed to compare, measure, calculate and evaluate thousands of readings in an extremely short period of time. Also, nations of the world are now adopting the computer system for security purposes. Many countries maintain a comprehensive database of their citizens for information and security reasons.
One of the distinguishing characteristics of nationhood is a state’s ability to provide security for her citizens, defend her sovereignty and territorial integrity. This is the minimum requirement for a nation to build a solid prosperous economy and begin the ultimate match towards social and political well being encapsulated as national interest. At the core of a complex policy aimed at achieving safety by defending sovereignty and maintaining territorial integrity, national security is therefore a grand policy to achieve, sustain and maintain a state of national survival. National security seeks first and foremost to guarantee internal cohesion, maintain law and order and ensure safety of citizens’ lives and property as well as guide against state vulnerability to internal insurrections and external aggression.
A state security database model is a database application that enables the data of every citizen in a state to be captured such that in the case of a crime investigation, reference can be made to the system to track down offenders or suspects. It is an application of the computer system and database in a positive direction to aid security investigations and verification of identity.
1.1 Statement of problem
Law enforcement agencies such as the Nigeria Police force is faced with the challenge of not having a system that is able to provide needed information on the profile of suspects involved in a crime or the verification of identity. As such, needed information to aid investigation is not easily obtained. To overcome this problem, it is important that a database model is in place to enable the capturing of the identity of the citizens to aid investigation and verification needs.
1.2 Objectives of the study
The following are the objectives of the study:
- To develop a state security database system
- To understand the concept of database and its different models
- To showcase the application of computers in state security
- To present the need and benefits of a state security database model
1.4 scope of the study
This study covers the development of a state security database model using the Nigerian Police Force as a case study. It covers the concept of database, the models and the application of computers in state security.
1.5 significance of the study
The significance of the study is that it will provide a system that will aid security and law enforcement bodies to get relevant information pertaining to any citizen that is involved in any crime. It will facilitate the capturing and easy retrieval of information pertaining to citizens or members of a state.
1.6 Definition of terms
Security: precautions taken to keep somebody or something safe from crime, attack, or danger
Database:
a systematically arranged collection of computer data, structured so that it can be automatically retrieved or manipulated
Investigation an examination or inquiry into something, especially a detailed one that is undertaken officially, or the act of undertaking an examination
Crime; an action prohibited by law or a failure to act as required by law
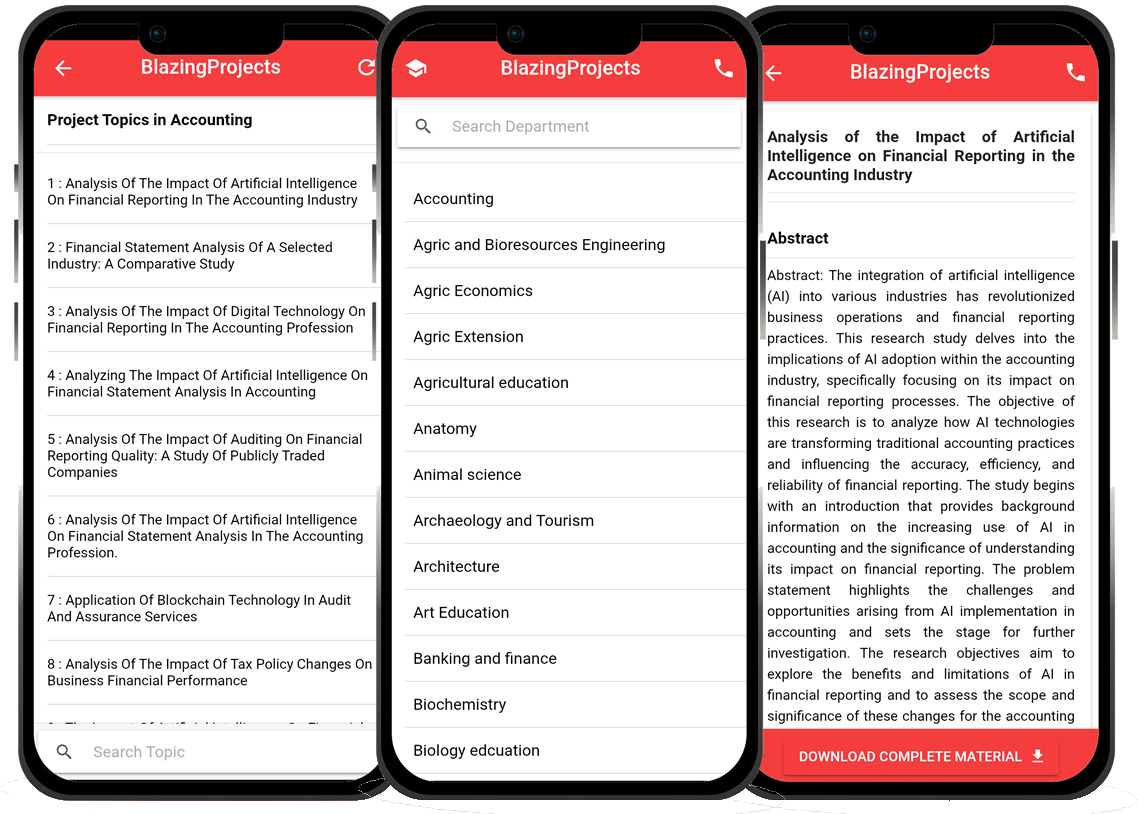
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Applying Machine Learning Techniques to Detect Financial Fraud in Online Transaction...
The project titled "Applying Machine Learning Techniques to Detect Financial Fraud in Online Transactions" aims to address the critical issue of detec...
Anomaly Detection in IoT Networks Using Machine Learning Algorithms...
The project titled "Anomaly Detection in IoT Networks Using Machine Learning Algorithms" focuses on addressing the critical challenge of detecting ano...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project titled "Applying Machine Learning Algorithms for Predicting Stock Market Trends" aims to explore the application of machine learning algor...
Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data...
The project titled "Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data" focuses on utilizing machine learning algorithms...
Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project titled "Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems" focuses on leveraging machine learning techniques ...
Implementation of a Machine Learning Algorithm for Predicting Stock Prices...
The project, "Implementation of a Machine Learning Algorithm for Predicting Stock Prices," aims to leverage the power of machine learning techniques t...
Development of an Intelligent Traffic Management System using Machine Learning Algor...
The project titled "Development of an Intelligent Traffic Management System using Machine Learning Algorithms" aims to revolutionize the traditional t...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
No response received....
Applying Machine Learning for Intrusion Detection in IoT Networks...
The project titled "Applying Machine Learning for Intrusion Detection in IoT Networks" aims to address the increasing cybersecurity threats targeting ...