Design and implementation of an intrusion tolerant system
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Intrusion Tolerant Systems2.2 History of Intrusion Tolerance
2.3 Key Concepts in Intrusion Tolerance
2.4 Types of Intrusion Tolerance Techniques
2.5 Challenges in Implementing Intrusion Tolerant Systems
2.6 Case Studies on Intrusion Tolerant Systems
2.7 Best Practices in Intrusion Tolerance
2.8 Future Trends in Intrusion Tolerant Systems
2.9 Comparison with Other Security Measures
2.10 Ethical and Legal Considerations in Intrusion Tolerance
Chapter THREE
3.1 Research Methodology Overview3.2 Research Design and Approach
3.3 Data Collection Methods
3.4 Sampling Techniques
3.5 Data Analysis Procedures
3.6 Research Validity and Reliability
3.7 Ethical Considerations in Research
3.8 Limitations of Research Methodology
Chapter FOUR
4.1 Data Analysis and Interpretation4.2 Findings on Intrusion Tolerant System Implementation
4.3 Discussion on Effectiveness of Intrusion Tolerance Techniques
4.4 Comparison of Intrusion Tolerance with Traditional Security Measures
4.5 Impact of Intrusion Tolerance on System Performance
4.6 Recommendations for Implementing Intrusion Tolerant Systems
4.7 Future Research Directions in Intrusion Tolerance
4.8 Implications of Findings on Cybersecurity Landscape
Chapter FIVE
5.1 Summary of Findings5.2 Conclusions Drawn from the Study
5.3 Contributions to the Field of Intrusion Tolerance
5.4 Practical Implications and Recommendations
5.5 Reflection on the Research Process
Thesis Abstract
AbstractIntrusion tolerance has emerged as a critical area of research in the field of cybersecurity to enhance the resilience of systems against sophisticated attacks. This research project focuses on the design and implementation of an intrusion-tolerant system that can effectively detect, tolerate, and recover from various types of intrusions. The system employs a multi-layered approach that combines intrusion detection mechanisms with fault tolerance techniques to ensure continuous operation even in the presence of intrusions. The design phase of the system involves the identification of critical system components, potential vulnerabilities, and attack scenarios to develop appropriate intrusion detection strategies. Various intrusion detection techniques such as signature-based detection, anomaly detection, and behavior analysis are integrated into the system to detect known and unknown attacks. In addition, the system incorporates redundancy and diversity at different levels to mitigate the impact of intrusions and enhance the system's fault tolerance capabilities. The implementation phase of the system focuses on the integration of intrusion detection mechanisms with fault tolerance strategies to create a comprehensive intrusion-tolerant architecture. The system is designed to dynamically adapt its security mechanisms based on the detected intrusions to prevent further damage and ensure system availability. Moreover, the system utilizes proactive recovery mechanisms such as checkpointing, replication, and reconfiguration to restore the system to a secure state after an intrusion event. To evaluate the effectiveness of the intrusion-tolerant system, a series of experiments are conducted using different types of intrusion scenarios and attack vectors. The system's performance in terms of intrusion detection accuracy, fault tolerance capabilities, and recovery efficiency is analyzed to assess its overall resilience against intrusions. The experimental results demonstrate that the intrusion-tolerant system is capable of effectively detecting and mitigating various types of intrusions while maintaining system availability and integrity. Overall, the design and implementation of an intrusion-tolerant system present a proactive approach to enhancing system security and resilience in the face of evolving cyber threats. By combining intrusion detection mechanisms with fault tolerance strategies, the system can effectively detect, tolerate, and recover from intrusions to ensure the continuous operation of critical systems in hostile environments.
Thesis Overview
INTRODUCTION
1.1 INTRODUCTION
Most current information systems are connected to the Internet for efficiency and convenience. However, the growth of accessibility makes the systems vulnerable to attackers. A web server is a program that runs over the Hyper Text Transfer Protocol which has client-server mode to serve clients with files and other details which are stored on the server. The web server is currently the most widely deployed type of distributed data server. Every computer on the internet that contains a website must have a web server program. Web servers are providing dynamic contents rather than static ones which have opened up many security flaws.With the development and scope of cloud computing, there is a tremendous shift in the web hosting industries. Most users prefer a server in the cloud due to ease of maintenance and low cost of infrastructure thus there is a great need to ensure the integrity and confidentiality of the systems we use. For this reason, many studies have been conducted in order to improve security of information systems. To protect the private keys of web servers and certificate authority, (Boneh et al, 1999) shared the keys among a number of share servers.
1.2 BACKGROUND OF THE STUDY
A dependable system is defined as one that is able to deliver a service that can justifiably be trusted; attributes of dependability include avaliablity ( readiness for correct service), reliablility (continuity of correct service), confidentiality (prevention of unauthorised disclosure of information), and integrity (absence of improper system state alterations)(Avizenis et al, 2001).
Large network infrastructures, such as the Internet, are vital for citizens to benefit from the services provided by theZ Information Society. However, users must be able to trust the services offered to them. MAFTIA (Randell et al, 2003), an European Union funded project investigated a comprehensive approach for tolerating both accidental faults and malicious attacks in large-scale distributed systems, thereby enabling them to remain operational during attack, without requiring time-consuming and potentially error-prone human intervention. SITAR (Sargor et al, 2001) uses commercial-off-the-shell servers to provide intrusion tolerance to distributed systems.
Emerging applications like electronic commerce and secure communications over open networks have made clear the fundamental role of public key cryptography as unique security solutions. On the other hand, these solutions clearly expose the fact that the protection of private keys is a security bottleneck in these sensitive applications. This problem is further worsened in the cases where a single and unchanged private key must be kept secret for very long time (such is the case of certification authority keys, and e-cash keys).
When classified information is sent electronically from one individual to another, some form of encryption must be used to protect the information from prying eyes. Because internet technology relies on the transmission of data through the public domain, this encryption is absolutely essential to preserving the security of electronically-transmitted information. Public key encryption, which was first developed in the 1970s, has gradually come to dominate the “cryptology market” because of its innate advantages over private-key methods of encrypting data; unlike its counterpart, public key encryption does not require that individuals share a secret key.
Although public key encryption algorithms such as RSA (Rivest et al, 1977) have achieved universal acceptance in the modern cryptology arena, they remain vulnerable to many potential security threats. For example, because public key encryption involves the “receiver” providing a public key to any “senders” who wish to send him confidential information (the receiver uses a different, private key to decrypt the data), it is entirely possible for a devious individual to send an encrypted message to the receiver that appears to have been sent from someone else; after all, the public key used to encrypt this message is fully available to everyone. In other words, when constructed improperly, public encryption systems such as RSA do not intrinsically protect against false sender identification.
1.3 STATEMENT OF THE PROBLEM
The computer security problem includes lots of buggy and insecure applications. Attackers can infect your system with malware and steal credentials like credit card details, passwords etc. Example of this is a malware called SilentBanker. It appends itself to your computer and stays silent. Now anytime your computer makes a web request to port 80 or 443 it monitors the request. Though port 443 is encrypted using SSL it doesn’t bother the malware. The malware injects malicious javascript to the target page to change it so whenever you type your password for authentication the password would get sent to the attacker. This malware was used to steal a lot of passwords from UK banks.
An attacker can steal your IP address and use it to send spam messages. An attacker does this to protect himself and shift the blame to the person whose computer he uses to send the spam messages. There are organizations that provide Denial of Service as a service. That is they can attack a web page or web server for a fee you pay. They do this by bombarding either a web server or web page with a lot of requests than it can process.
Nowadays, we see the spread of war from physical space to the cyber space. An example of this is the Stuxnet virus (2008) which the NSA and Israeli Intelligence agencies used in shutting down Iran’s nuclear power plant. What the attackers did was that they use four zero day windows exploit to infect the computer of the administrator that maintains the nuclear facility. This exploits just sits on your windows computer and only functions if you have the Siemens PCS 7 SCADA control software on your windows computer. It will wait for your to connect the Siemens controller to the network then it will affect the network. This malware in the target computers serves as logic bombs. They used this to attack the nuclear plant thereby shutting down a billion dollar project with just a malware.
Snowden (2013), an NSA whistleblower released a top secret espionage carried out by US and British Intelligence agencies in which they intercept over 80% of web traffics from sites like Facebook, Google, Twitter etc. and store this information to be used for various activities. This revelations together with the ones from whistleblowing site WikiLeaks made aware of the insecurity of the web which we depend so greatly for our daily activities.
More recently, we were made aware that some Nigerian governors use the exploits of the malware firm Hacking Team. Hacking Team is a legal malware company that creates exploit used to attack varieties of devices ranging from web servers, computers and anything you can think of. This exposes the fact that in Nigeria today there are people who poses this weaponized- cyber tools that can be used to access virtually almost all devices and steal information, plant information for the purpose of implicating the target.
Noting this problems we face in this modern era, we turn to cryptography. Cryptography is used to encrypt data so it can only be read by the person who has the secret key. So, even though an attacker breaks into our system he cannot decode our information.
1.4 AIM AND OBJECTIVES OF STUDY
Despite the use of public key cryptography in simplifying encryption processes, we are still stuck with security bottlenecks. Now we see advanced viruses, worms, Trojans etc. Most applications are not implemented correctly. The goal of this project includes
- To analyze some versions of RSA implemented in HTTPS.
- To show the strengths and weaknesses of RSA. Some common attacks on it.
- To show how RSA cryptosystem can be used correctly to build intrusion tolerant application that can function correctly even when attacked.
- To design a version of RSA cryptosystem which is tamper-resistant and can be used for encryption, session setup etc.
- To develop a software based on this design.
1.5 SIGNIFICANCE OF THE STUDY
RSA is the most widely used public key cryptosystem. It is used for encryption, session startups, implementing digital signatures and many others. It is implemented in our smart cards, the operating system we use and the browsers we use for surfing the internet etc. However over the years versions of RSA implemented in WEP, HTTP etc has been broken. This project analysis the security of RSA in WEB, HTTP etc and also covers attacks on RSA, and at the end designing and implement a version of RSA that is intrusion tolerant.
1.6 SCOPE OF THE STUDY
This project covers ITTC (Boneh et al, 1999), an intrusion tolerant application that uses RSA for encryption. ITTC is a projects that protects the private keys of web servers and certificate authorities by splitting server into smaller share servers so that even if the attacker penetrates a few of the servers he cannot compromise the whole system. Also, I discussed about SITAR (Sargor et al, 2001) a DARPA-funded research project that investigates the intrusion tolerance in distributed system to provide reliable services. I showed some attacks on RSA like the binding attack, common modulus attack etc. and I also analyzed security problems of some versions of RSA like the PKCS1 etc. I also showed how to design and implemented RSA correctly.
1.7 LIMITATIONS OF THE STUDY
The main limitation is that I could not access specialized hardware suitable for RSA. Most specialized RSA implementation are implemented in both hardware and software. Also I did not cover properly its use in environments like smart cards because of limited tools to analysis security in these environments.
1.8 DEFINITION OF TERMS
This are the meaning of keywords used in the project:
- ITTC: Intrusion Tolerant via Threshold Cryptography
- MAFTIA: Malicious and Accidental Fault Tolerance for Internet Applications
- COTS: Commercial Off the Shelf
- SITAR: Scalable Intrusion Tolerant Architecture
- DPASA: Designing Protections and Adaptation into a Survivability Architecture
- PKI: Public Key Infrastructure
- SCIT: Self Cleansing Intrusion Tolerance
- ACT: Adaptive Cluster Transformation
- MAC: Message Authentication Code
10. RSA:Rivest Shamir Adleman
11. CA: Certificate Authority
12. MD5: Message Digest 5
13. RFITS: Randomized Failover Intrusion Tolerant System.
This are the definition of some of the terms used in this project.
- PUBLIC KEY CRYPTOGRAPHY: This is a cryptography in which a pair of keys is used to encrypt and decrypt a message. The public key is used to encrypt the message, while the private key is used to decrypt the cipher-text.
- CRYPTOSYSTEM: This refers to a suite of cryptographic algorithms needed to implement a particular security service. Typically it consists of three algorithms, one for key generation, one for encryption, and one for decryption.
- THRESHOLD CYPTOSYSTEM: A cryptosystem is threshold if in order to decrypt an encrypted message, several parties must cooperate in the decryption protocol.
- CRYPTOGRAPHY: This is the practice and study of techniques for secure communication in the presence of third parties.
- CRYPTANALYSIS: This is the study of techniques used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown.
- SYMMETRIC-KEY ALGORITHMS: These are algorithms for cryptography that use the same cryptographic keys for both encryption of plaintext and decryption of cipher-text
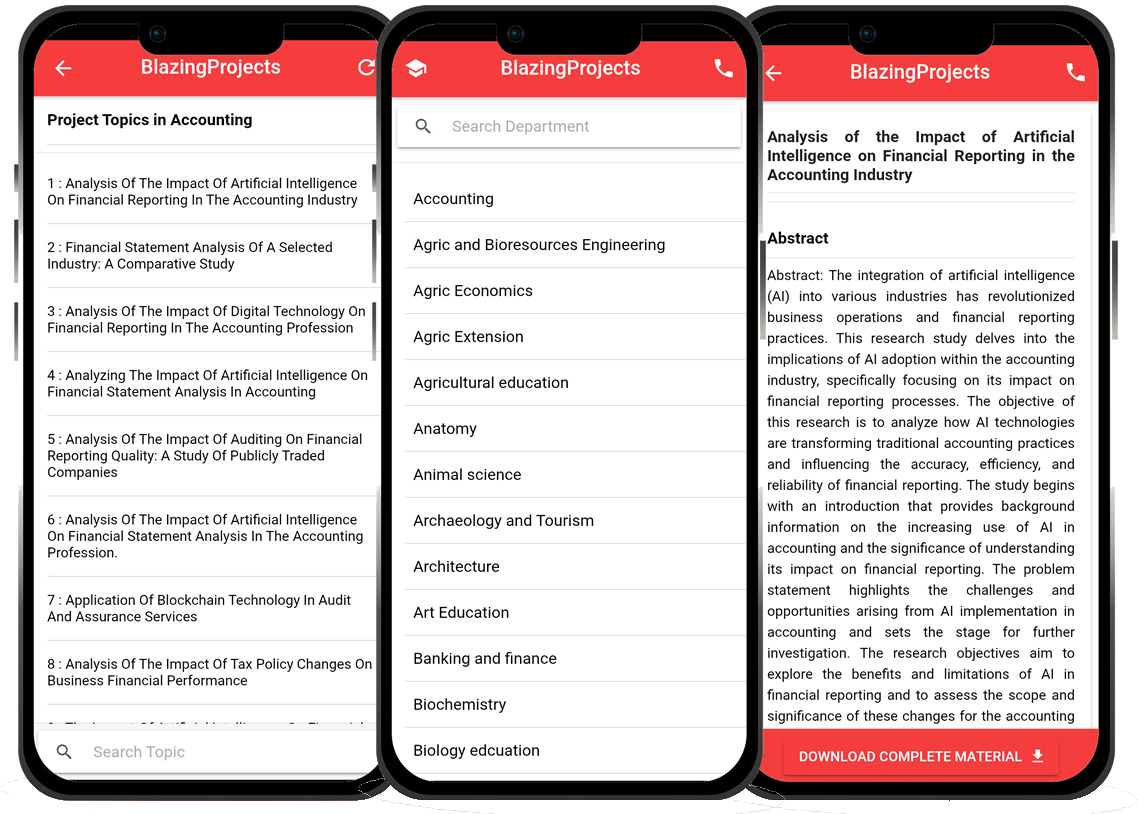
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Applying Machine Learning Techniques to Detect Financial Fraud in Online Transaction...
The project titled "Applying Machine Learning Techniques to Detect Financial Fraud in Online Transactions" aims to address the critical issue of detec...
Anomaly Detection in IoT Networks Using Machine Learning Algorithms...
The project titled "Anomaly Detection in IoT Networks Using Machine Learning Algorithms" focuses on addressing the critical challenge of detecting ano...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project titled "Applying Machine Learning Algorithms for Predicting Stock Market Trends" aims to explore the application of machine learning algor...
Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data...
The project titled "Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data" focuses on utilizing machine learning algorithms...
Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project titled "Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems" focuses on leveraging machine learning techniques ...
Implementation of a Machine Learning Algorithm for Predicting Stock Prices...
The project, "Implementation of a Machine Learning Algorithm for Predicting Stock Prices," aims to leverage the power of machine learning techniques t...
Development of an Intelligent Traffic Management System using Machine Learning Algor...
The project titled "Development of an Intelligent Traffic Management System using Machine Learning Algorithms" aims to revolutionize the traditional t...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
No response received....
Applying Machine Learning for Intrusion Detection in IoT Networks...
The project titled "Applying Machine Learning for Intrusion Detection in IoT Networks" aims to address the increasing cybersecurity threats targeting ...