Design and implementation of encrypted data base system
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Encryption Technologies2.2 Historical Development of Encryption
2.3 Types of Encryption Algorithms
2.4 Encryption in Database Systems
2.5 Security Threats in Database Systems
2.6 Encryption Key Management
2.7 Implementation of Encrypted Database Systems
2.8 Case Studies on Encrypted Database Systems
2.9 Comparison of Encryption Techniques
2.10 Future Trends in Encrypted Database Systems
Chapter THREE
3.1 Research Design3.2 Data Collection Methods
3.3 Sampling Techniques
3.4 Data Analysis Procedures
3.5 Research Instruments
3.6 Ethical Considerations
3.7 Validity and Reliability
3.8 Limitations of Research Methodology
Chapter FOUR
4.1 Overview of Research Findings4.2 Analysis of Data Collected
4.3 Interpretation of Results
4.4 Comparison with Existing Literature
4.5 Implications of Findings
4.6 Recommendations for Practice
4.7 Recommendations for Future Research
4.8 Contributions to Knowledge
Chapter FIVE
5.1 Summary of Findings5.2 Conclusions
5.3 Contributions to the Field
5.4 Practical Applications
5.5 Limitations of the Study
5.6 Recommendations for Implementation
5.7 Suggestions for Further Research
5.8 Conclusion
Thesis Abstract
AbstractWith the increasing concerns over data security and privacy, the design and implementation of an encrypted database system have become crucial in safeguarding sensitive information. This research project focuses on developing a secure database system that integrates encryption techniques to protect data at rest and in transit. The encrypted database system is designed to provide confidentiality, integrity, and availability of data by utilizing encryption algorithms such as Advanced Encryption Standard (AES) and Rivest-Shamir-Adleman (RSA). Data encryption at rest ensures that stored information remains secure from unauthorized access, while encryption in transit protects data as it is transmitted between the database and applications. In addition to encryption, key management plays a vital role in maintaining the security of the database system. Secure key generation, storage, and distribution methods are implemented to prevent key compromise and unauthorized decryption of sensitive data. Access controls and user authentication mechanisms are also integrated to restrict database access to authorized personnel only. The implementation of the encrypted database system involves developing secure data storage mechanisms and secure communication protocols between the database server and client applications. Encryption keys are securely managed to prevent key leakage and ensure the confidentiality of the encrypted data. Performance evaluation of the encrypted database system includes assessing the impact of encryption on database operations such as data insertion, retrieval, and updates. The system's efficiency and overhead in terms of computational resources and response time are analyzed to ensure that encryption does not significantly degrade database performance. Furthermore, the encrypted database system is tested for resilience against various security threats such as unauthorized access, data breaches, and cyber-attacks. Vulnerability assessments and penetration testing are conducted to identify and mitigate potential security vulnerabilities in the system. Overall, the design and implementation of the encrypted database system aim to provide a secure and reliable platform for storing and managing sensitive information. By integrating encryption techniques, key management, access controls, and user authentication, the system enhances data security and privacy, ensuring that confidential data remains protected from unauthorized access and breaches.
Thesis Overview
1.0 INTRODUCTION
In the past, security was simply a matter of locking the door or storing files in a locked filing cabinet or safe. Today, paper is no longer the only medium of choice for housing information. Files are stored in computer databases as well as file cabinets. Hard drives and floppy disks hold many of our secret information..
In the physical world, security is a fairly simple concept. If the locks on your house’s doors and windows are so strong that a thief cannot break in to steal your belongings, the house is secure. For further protection against intruders breaking through the locks, you might have security alarms. Similarly, if someone tries to fraudulently withdraw money from your bank account but the teller asks for identification and does not trust the thief’s story, your money is secure. When you sign a contract with another person, the signatures are the legal driving force that impels both parties to honor their word.
In the digital world, security works in a similar way. One concept is privacy, meaning that no one can break into files to read your sensitive data (such as medical records) or steal money (by, for example, obtaining credit card numbers or online brokerage accounts information). Privacy is the lock on the door. Another concept, data integrity, refers to a mechanism that tells us when something has been altered. That’s the alarm. By applying the practice of authentication, we can verify identities. That’s comparable to the ID required to withdraw money from a bank account (or conduct a transaction with an online broker). And finally, non repudiation is a legal driving force that impels people to honor their word.
As the Internet becomes a more pervasive part of daily life, the need for e-security becomes even more critical. Any organization engaged in online activity must assess and manage the e-security risks associated with this activity. Effective use of cryptographic techniques is at the core of many of these risk-management strategies. The most important security tool is cryptography.
1.1
BACKGROUND OF THE STUDY
Before the modern era, cryptography was concerned solely with message confidentiality (i.e., encryption) “ conversion of messages from a comprehensible form into an incomprehensible one, and back again at the other end, rendering it unreadable by interceptors or eavesdroppers without secret knowledge (namely, the key needed for decryption of that message). In recent decades, the field has expanded beyond confidentiality concerns to include techniques for message integrity checking, sender/receiver identity authentication, digital signatures, interactive proofs, and secure computation, amongst others.
Encryption attempts to ensure secrecy in communications, such as those of spies, military leaders, and diplomats, but it have also had religious applications.
Steganography (i.e., hiding even the existence of a message so as to keep it confidential) was also first developed in ancient times. An early example, from Herodotus, concealed a message – a tattoo on a slave’s shaved head – under the regrown hair. More modern examples of steganographyk include the use of invisible ink, microdots, and digital watermarks to conceal information.
1.2 STATEMENT OF THE PROBLEM
The problem is security. The password method used in almost all commercial operating systems is probably not very strong against a sophisticated or unsophisticated attacker. The choice of data encryption comes next in the minds of those that want reduction of unauthorized access on confidential files or data.
Security provided by the computer operating systems come with a preset super user account and password. The super user may have a password to control network functionality, another to conduct or access nightly backups, create accounts, and so on. For a cracker, logging on to a system as the super user is possibly the best way to collect data or do damage. If the super user has not changed an operating system’s preprogrammed passwords, the network is vulnerable to attack. Most crackers know these passwords, and their first attempt to break into a network is simply to try them. If an attacker cannot log on as the super user, the next best thing might be to figure out the user name and password of a regular user. It is used to be standard practice in most Universities and colleges, and in some commercial companies, to assign every student or employee an account with user name and initial password the password being the user name. Everyone was instructed to log on and change the password, but often, hackers and crackers logged on before legitimate users had a chance.
1.3 OBJECTIVES OF THE STUDY
a. To understand and improve the computer data security through encryption of data.
b. To provide a means of safeguarding data in a system
c. To enhance the integrity of data
d. To facilitate the use of more sopheasted tool against hacking, cracking, bugging of a system.
e. To develop a platform to complement physical security.
1.4 SIGNIFICANCE OF THE STUDY
Data security in these contemporary times is a must. For your secrets to be secure, it may be necessary to add protections not provided by your computer operating systems. The built-in protections may be adequate in some cases. If no one ever tries to break into or steal data from a particular computer, its data will be safe. Or if the intruder has not learned how to get around the simple default mechanisms, they’re sufficient. But many attackers do have the skills and resources to break various security systems. If you decide to do nothing and hope that no skilled cracker targets your information, you may get lucky, and nothing bad will happen.
One of the most important tools for protecting your data from an authorized access is Data Encryption, any of various methods that are used to turn readable files into gibberish. Even if an attacker obtains the contents of the file, it is gibberish. It does not matter whether or not the operating system protections worked.
1.5 LIMITATIONS OF THE STUDY
Technology constraint: The problem encountered here is searching information about computer security through Data Encryption and Key Hash Algorithm and another problem is since the secret key has to be send to the receiver of the encrypted data, it is hard to securely pass the key over the network to the receiver.
Time constraint: the time giving for the submission of this project work was not really enough for the researcher to extensively carry out more research on this work.
Financial constraint: there was not enough money to extensively carry out this work.
1.6 SCOPE OF THE STUDY
Computer Security has been defined as the art of protecting computer system and information from harm and unauthorized use .the most important security tool beyond human integrity used is cryptography. which is used to hide data from public view and to ensure that the integrity and privacy of any data sent across a network is not compromised. cryptography involves encryption and decryption process .the scope of this study covers the message security ,message integrity, user authentication and key management of messages.
1.6 DEFINITION OF TERMS
SECURITY: The set of accesses controls and permission that are used to determine if a server can grant a request for a service or resource from a client.
PASSWORD: An identity that defines an authorized users of a computer in order to access to the system.
SOFTWARE: A collection of computer programs that runs as a group to accomplish a set of objectives which could be referred to as job.
SYSTEM: An organized unit which composed of two or more inter related parts that functions together to achieve a particular goal.
ENCRYPTION: The process of converting ordinary information (plaintext) into unintelligible gibberish (that is, cipher text).
DECRYPTION: The reverse, moving from unintelligible cipher text to plain text.
ALOGRITM: This is a sequential way of solving a problem.
CRYPTOGRAPHY: This is used to hide data from public view and to ensure that the integrity and privacy of any data sent across a network has not been compromised
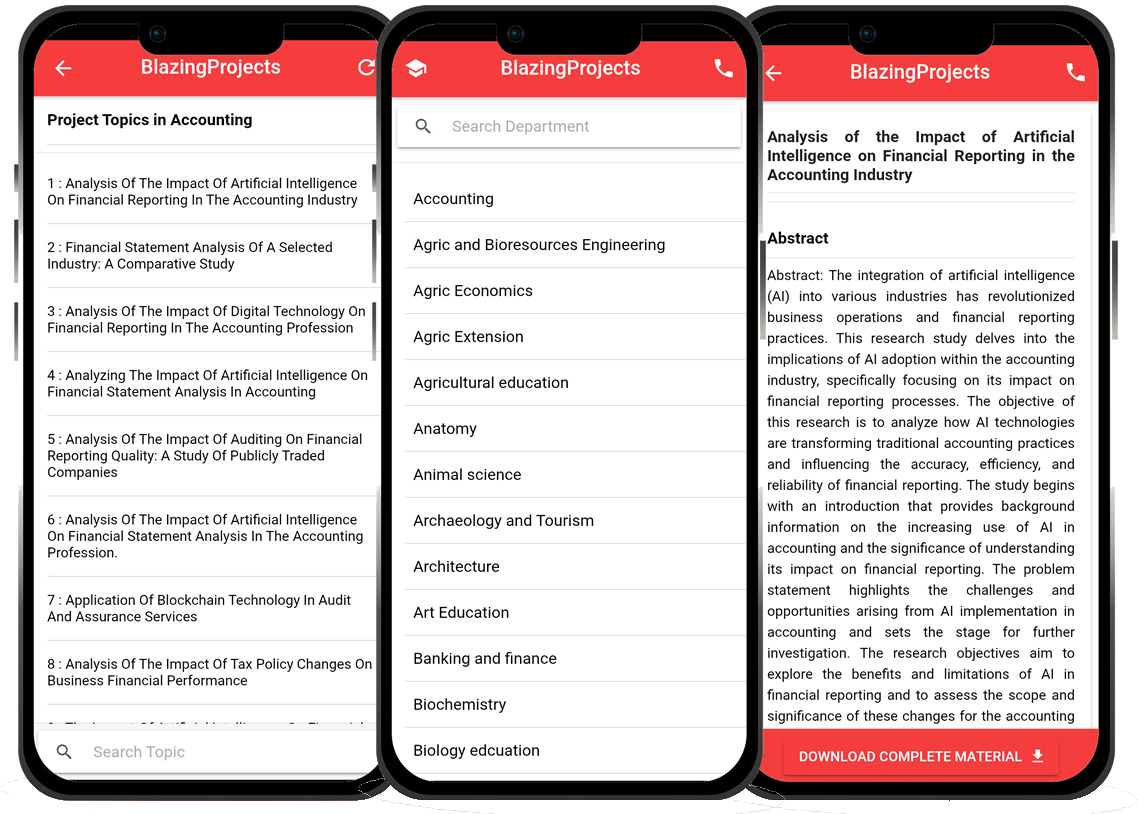
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Applying Machine Learning Techniques to Detect Financial Fraud in Online Transaction...
The project titled "Applying Machine Learning Techniques to Detect Financial Fraud in Online Transactions" aims to address the critical issue of detec...
Anomaly Detection in IoT Networks Using Machine Learning Algorithms...
The project titled "Anomaly Detection in IoT Networks Using Machine Learning Algorithms" focuses on addressing the critical challenge of detecting ano...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project titled "Applying Machine Learning Algorithms for Predicting Stock Market Trends" aims to explore the application of machine learning algor...
Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data...
The project titled "Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data" focuses on utilizing machine learning algorithms...
Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project titled "Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems" focuses on leveraging machine learning techniques ...
Implementation of a Machine Learning Algorithm for Predicting Stock Prices...
The project, "Implementation of a Machine Learning Algorithm for Predicting Stock Prices," aims to leverage the power of machine learning techniques t...
Development of an Intelligent Traffic Management System using Machine Learning Algor...
The project titled "Development of an Intelligent Traffic Management System using Machine Learning Algorithms" aims to revolutionize the traditional t...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
No response received....
Applying Machine Learning for Intrusion Detection in IoT Networks...
The project titled "Applying Machine Learning for Intrusion Detection in IoT Networks" aims to address the increasing cybersecurity threats targeting ...