Design and implementation of a web based crime records information system
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Crime Records Information Systems2.2 Evolution of Crime Records Management
2.3 Importance of Technology in Crime Data Management
2.4 Existing Crime Records Information Systems
2.5 Advantages and Disadvantages of Web-based Systems
2.6 Cybersecurity in Crime Data Management
2.7 Data Analytics in Crime Prevention
2.8 User Interface Design for Crime Records Information Systems
2.9 Accessibility and Usability of Crime Data Systems
2.10 Trends in Crime Data Management Technologies
Chapter THREE
3.1 Research Methodology Overview3.2 Research Design and Approach
3.3 Data Collection Methods
3.4 Sampling Techniques
3.5 Data Analysis Tools and Techniques
3.6 Ethical Considerations
3.7 Validity and Reliability of Data
3.8 Limitations of the Research Methodology
Chapter FOUR
4.1 Data Analysis and Interpretation4.2 Demographic Analysis of Crime Data
4.3 Crime Trends and Patterns Identified
4.4 Comparison with Existing Systems
4.5 User Feedback and System Performance
4.6 Recommendations for System Improvement
4.7 Implications of Findings
4.8 Future Research Directions
Chapter FIVE
5.1 Summary of Findings5.2 Conclusion
5.3 Contributions to the Field
5.4 Practical Implications
5.5 Recommendations for Implementation
5.6 Areas for Future Research
5.7 Reflections on the Research Process
5.8 Conclusion and Final Remarks
Thesis Abstract
This study, design and implementation of web based crime records system, is centered on using web applications to enable an easy, secured and fast way reporting crime and complaints. Chapter one x-rayed the aim of the project which is centered understanding the research work and presenting a statement of problem, and ensuring that objectives address the stated problems. Chapter two focused on literature review; gives a detailed and adept description on the project topic, with explanations of concepts related to the study from works done by a variety of intellectual authors. Chapter three presents the methodology and analysis of the existing system. It also presents a detailed analysis of the proposed system and how it will overcome the weaknesses of the existing system. Chapter four describes the design and implementation of the proposed system. This is where all the major work was put into in order to accomplish the desired result of the proposed system. It basically centered on what the input-output specifications of the system will portray, various diagrams to show the activities and processes of the system, flowcharts to describe the operation of the system, and the needed software and hardware requirements to ensure that the system works among others.
Thesis Overview
Security is the most vital aspect of every society all over the globe irrespective of the location. Conventionally the management of records and profile is in our police stations are done manually by writing on paper, filing and categorizing the collected data and storing them in a cabinet or shelves. This method is slow and painstaking as retrieval of this data involves searching through hundreds or thousands of files to retrieve a small piece of information depending on the size of institution.
With the introduction of computers and Information System (IS), the process of collection and management of data which involved record keeping and profile management in police stations has been tremendously improved as the speed of data collecting and retrieval increased significantly thereby making data management is a major driving force in the ongoing Information Technology (IT) revolution. The records of citizens (complainant/defendant) collected serve many purposes and pass through many corporate processes. The records are so important that the police channel much resource to preserve the integrity of the records.
However, over the last few decades, there has been significant improvement in data storage, data access, data protection and data distribution where data storage was once at a high premium that a single CD-ROM can now store 500MB of data. Rumours has it next generation of CD-ROMs will store at least ten times that amount but there has been challenges in the last few years to the traditional data security and access philosophies. The lessons learnt over the years show that the continuing importance of data and the increase in citizens’ records and profile no matter how it is accessed or packaged will undoubtedly play a central role in the health and competitiveness of police in the future, (Alter, 2002).
The history of information systems coincides with the history of computer science that began long before the modern discipline of computer science emerged in the twentieth century. Regarding the circulation of information and ideas, numerous legacy information systems still exist today that are continuously updated to promote ethnographic approaches, to ensure data integrity, and to improve the social effectiveness and efficiency of the whole process.
Before the concept of information systems was created, computer scientists were just programmers creating applications for science and math calculations. As computer usage evolved in fields of business and data management, software applications were needed to process nonscientific data
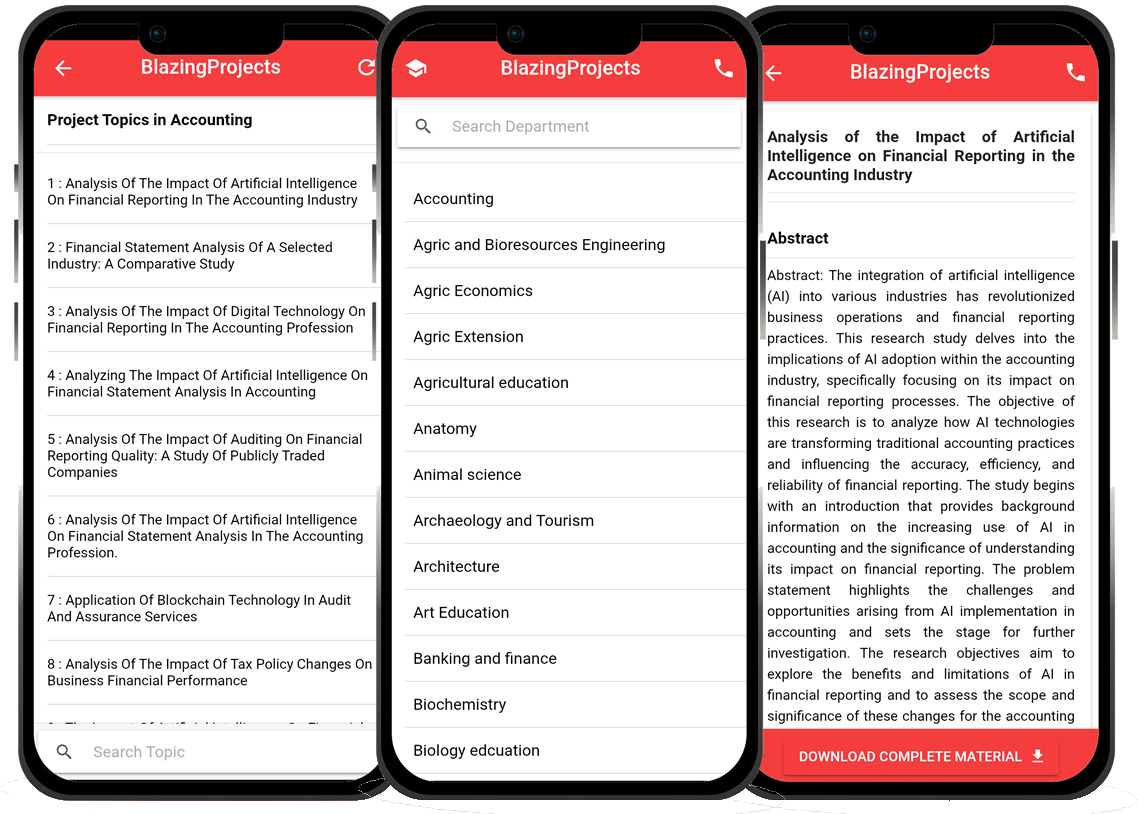
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Applying Machine Learning Techniques to Detect Financial Fraud in Online Transaction...
The project titled "Applying Machine Learning Techniques to Detect Financial Fraud in Online Transactions" aims to address the critical issue of detec...
Anomaly Detection in IoT Networks Using Machine Learning Algorithms...
The project titled "Anomaly Detection in IoT Networks Using Machine Learning Algorithms" focuses on addressing the critical challenge of detecting ano...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project titled "Applying Machine Learning Algorithms for Predicting Stock Market Trends" aims to explore the application of machine learning algor...
Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data...
The project titled "Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data" focuses on utilizing machine learning algorithms...
Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project titled "Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems" focuses on leveraging machine learning techniques ...
Implementation of a Machine Learning Algorithm for Predicting Stock Prices...
The project, "Implementation of a Machine Learning Algorithm for Predicting Stock Prices," aims to leverage the power of machine learning techniques t...
Development of an Intelligent Traffic Management System using Machine Learning Algor...
The project titled "Development of an Intelligent Traffic Management System using Machine Learning Algorithms" aims to revolutionize the traditional t...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
No response received....
Applying Machine Learning for Intrusion Detection in IoT Networks...
The project titled "Applying Machine Learning for Intrusion Detection in IoT Networks" aims to address the increasing cybersecurity threats targeting ...