Design and implementation of database management system case of an abiolian solution limited address book
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Database Management Systems2.2 Evolution of Database Management Systems
2.3 Types of Database Management Systems
2.4 Functions of Database Management Systems
2.5 Importance of Database Management Systems
2.6 Challenges in Database Management Systems
2.7 Trends in Database Management Systems
2.8 Comparison of Database Management Systems
2.9 Case Studies on Database Management Systems
2.10 Future of Database Management Systems
Chapter THREE
3.1 Research Methodology Overview3.2 Research Design Selection
3.3 Data Collection Methods
3.4 Sampling Techniques
3.5 Data Analysis Procedures
3.6 Research Instruments Used
3.7 Ethical Considerations
3.8 Limitations of the Methodology
Chapter FOUR
4.1 Data Analysis and Interpretation4.2 Findings on Database Management Systems
4.3 Comparison of Different Database Management Systems
4.4 Impact of Database Management Systems on Organizations
4.5 Recommendations for Database Management Systems Improvement
4.6 Implementing Database Management Systems Successfully
4.7 Future Prospects of Database Management Systems
4.8 Case Studies on Successful Database Management System Implementations
Chapter FIVE
5.1 Summary of Findings5.2 Conclusion of the Research
5.3 Recommendations for Future Research
5.4 Implications of the Study
5.5 Contribution to the Field
Thesis Abstract
AbstractThis research project focuses on the design and implementation of a database management system for an address book application developed for Abiolian Solution Limited. The address book system is intended to facilitate the storage and retrieval of contact information for employees and clients within the company. The database management system plays a crucial role in organizing and managing the vast amounts of data associated with the address book. The project employs a relational database model to structure the data in a logical and efficient manner. The database schema includes tables for storing information such as employee names, contact numbers, email addresses, and other relevant details. Additionally, the system incorporates relationships between tables to establish connections between different entities within the address book. The implementation of the database management system involves using MySQL as the relational database management system due to its robust features and compatibility with the application requirements. SQL queries are utilized to create, retrieve, update, and delete data from the database, ensuring seamless interaction with the address book application. Furthermore, the system incorporates security measures to protect sensitive information stored in the database. Access control mechanisms are implemented to restrict unauthorized users from modifying or accessing confidential data, thereby ensuring data integrity and confidentiality. The address book application developed for Abiolian Solution Limited demonstrates the practical implications of utilizing a well-designed database management system. The system enhances the efficiency of managing contact information and enables users to quickly retrieve relevant data when needed. Additionally, the relational database model provides a scalable and flexible structure that can accommodate future expansions and modifications to the address book system. Overall, the design and implementation of the database management system for the address book application at Abiolian Solution Limited showcases the importance of effective data organization and management in a business setting. By leveraging the capabilities of a relational database system, the company can streamline its operations, improve data accessibility, and enhance overall productivity.
Thesis Overview
INTRODUCTION
1.1 Background Of The Study
A database is an organized collection of data. It is the collection of schemas, tables, queries, reports, views, and other objects. The data are typically organized to model aspects of reality in a way that supports processes requiring information, such as modelling the availability of rooms in hotels in a way that supports finding a hotel with vacancies.
A database management system (DBMS) is a computer software application that interacts with the user, other applications, and the database itself to capture and analyze data. A general-purpose DBMS is designed to allow the definition, creation, querying, update, and administration of databases. Well-known DBMSs include MySQL, PostgreSQL, MongoDB, MariaDB, Microsoft SQL Server, Oracle, Sybase, SAP HANA, MemSQL and IBM DB2. A database is not generally portable across different DBMSs, but different DBMS can interoperate by using standards such as SQL and ODBC or JDBC to allow a single application to work with more than one DBMS. Database management systems are often classified according to the database model that they support; the most popular database systems since the 1980s have all supported the relational model as represented by the SQL language. Sometimes a DBMS is loosely referred to as a “database”.
Following the technology progress in the areas of processors, computer memory, computer storage, and computer networks, the sizes, capabilities, and performance of databases and their respective DBMSs have grown in orders of magnitude. The development of database technology can be divided into three eras based on data model or structure: navigational, SQL/relational, and post-relational.
The two main early navigational data models were the hierarchical model, epitomized by IBM’s IMS system, and the CODASYL model (network model), implemented in a number of products such as IDMS.
The relational model, first proposed in 1970 by Edgar F. Codd, departed from this tradition by insisting that applications should search for data by content, rather than by following links. The relational model employs sets of ledger-style tables, each used for a different type of entity. Only in the mid-1980s did computing hardware become powerful enough to allow the wide deployment of relational systems (DBMSs plus applications). By the early 1990s, however, relational systems dominated in all large-scale data processing applications, and as of 2015 they remain dominant: IBM DB2, Oracle, MySQL, and Microsoft SQL Server are the top DBMS.[10] The dominant database language, standardised SQL for the relational model, has influenced database languages for other data models.
Object databases were developed in the 1980s to overcome the inconvenience of object-relational impedance mismatch, which led to the coining of the term “post relational” and also the development of hybrid object-relational databases.
The next generation of post-relational databases in the late 2000s became known as NoSQL databases, introducing fast key-value stores and document-oriented databases. A competing “next generation” known as NewSQL databases attempted new implementations that retained the relational/SQL model while aiming to match the high performance of NoSQL compared to commercially available relational DBMSs (https://en.wikipedia.org/wiki/Database).
1.2 Statement Of The Study
The problem currently facing the organization such as my case study (Abiolian Solution Limited) is that they easy loss or don’t know exact where they record or keep the information of a client / customer.
Till date, organization still keeps their information and customer data using the manual method of using biro to write their information on books. This particular manual process of keeps or storing information are face with much problem and issue like the following:
- Difficulty in Retrieving of information / record
- Time wasting and occupy more space
- Important documents may be altered by an unauthorized personal
1.3 Significance Of The Study
The significance of this study includes the following:
- It helps in economic cost reduction in running a particular application.
- It provides humans with effective resource management.
- It will help organizations in focusing on core business in the sense that you only concentrate on what means most to you. Since your applications will be run over the internet, you do not have to worry about technical problems and other inconveniences associated with physical unified storage solution spaces.
- It increases performance and support by updating the fact that all your software and applications automatically.
- It provides security and compliance.
- It provides anytime anywhere access to information.
1.4 Objective of the study
The main objective of this project is to design and implement a database management system for Abiolian Solution Limited. The specific objectives are:
- To develop software that can be use to save customer information
- To increase resource availability of Cloud Computing system.
- To develop an address book application that will be launch as a cloud application.
- To develop application that can reduces stress of looking paper or book in which a particular customer is save.
1.5 Scope Of The Study
The scope of this proposed system is center on design and implementation of database management system for Abiolian Solution Limited address book.
1.6 Limitation Of The Study
Usually, every work has some limitations and this study is not exempted.
The two major limitations of this study are the high programming technique as well as financial constraints. The high programming technique constraint in PHP, JQUERY and MYSQL prevents the researcher to have an in depth study and analysis on the subject matter. While the issue of financial constraint limits the frequency of investigation to/from the institution toward gathering the necessary information relevant for the study.
1.7 Definition Of Terms
Cloud Computing: the practice of using a network of remote servers hosted on the Internet to store, manage, and process data, rather than a local server or a personal computer.
System: A method or set of procedures and even personnel working together as a whole to achieve a goal.
Data: This are numbers, text or images which are in a form suitable for storage in a computer or processed by a computer, or an incomplete information/ unprocessed information.
Information: This is a meaningful material derived from computer data by organizing it and interpreting it in a specific way.
Input: Data entered into the computer for storage or processing.
Output: Information produced from a computer after processing.
Information System: A set of interrelated components that collect (or retrieve), process, store, and distribute information to support decision making and control in an organization.
HTML CODE: HTML stands for Hyper Text Markup Language. It is a type of computer language that is primarily used for files that are posted on the internet and viewed by web browsers. HTML files can also be sent via email.
Markup language: A markup language is a combination of words and symbols which give instructions on how a document should appear. For example, a tag may indicate that words are written in italics or bold type.
Web browser: -A Web browser is a software program that interprets the coding language of the World Wide Web in graphic form, displaying the translation rather than the coding. This allows anyone to “browse the Web” by simple point and click navigation, bypassing the need to know commands used in software languages.
File extension: A file extension is the suffix at the end of a filename that tells a computer, and the computer user, which program is needed to open the file. Also called a filename extension, this suffix preceded by at least one period, is generally one to five characters long but the norm is usually three characters in length.
Email: Email, also sometimes written as e-mail, is simply the shortened form of electronic mail, a protocol for receiving, sending, and storing electronic messages. Email has gained popularity with the spread of the Internet. In many cases, email has become the preferred method of communication.
TCP/IP: This often used but little understood set of operations stands for Transmission Control Protocol/Internet Protocol. TCP/IP is the combination of the two and describes the set of protocols that allows hosts to connect to the Internet. In actuality, TCP/IP is a combination of “more than those two protocols, but the TCP and IP parts of TCP/IP are the main ones and the only ones to become part of the acronymthat describes the operations involved.
TEXT FILE: A text file is a computerfile that stores a typed document as a series of alphanumeric characters, usually without visual formatting information. The content may be a personal note or list, a journal or newspaper article, a book, or any other text that can be rendered accurately in typewritten form.
Hyper Link:-A hyperlink is a graphic or a piece of text in an Internet document that can connect readers to another webpage, or another portion of a document. Web users will usually find at least one hyperlink on every webpage. The simplest form of these is called embedded text or an embedded link.
WWW: acronym for World Wide Web
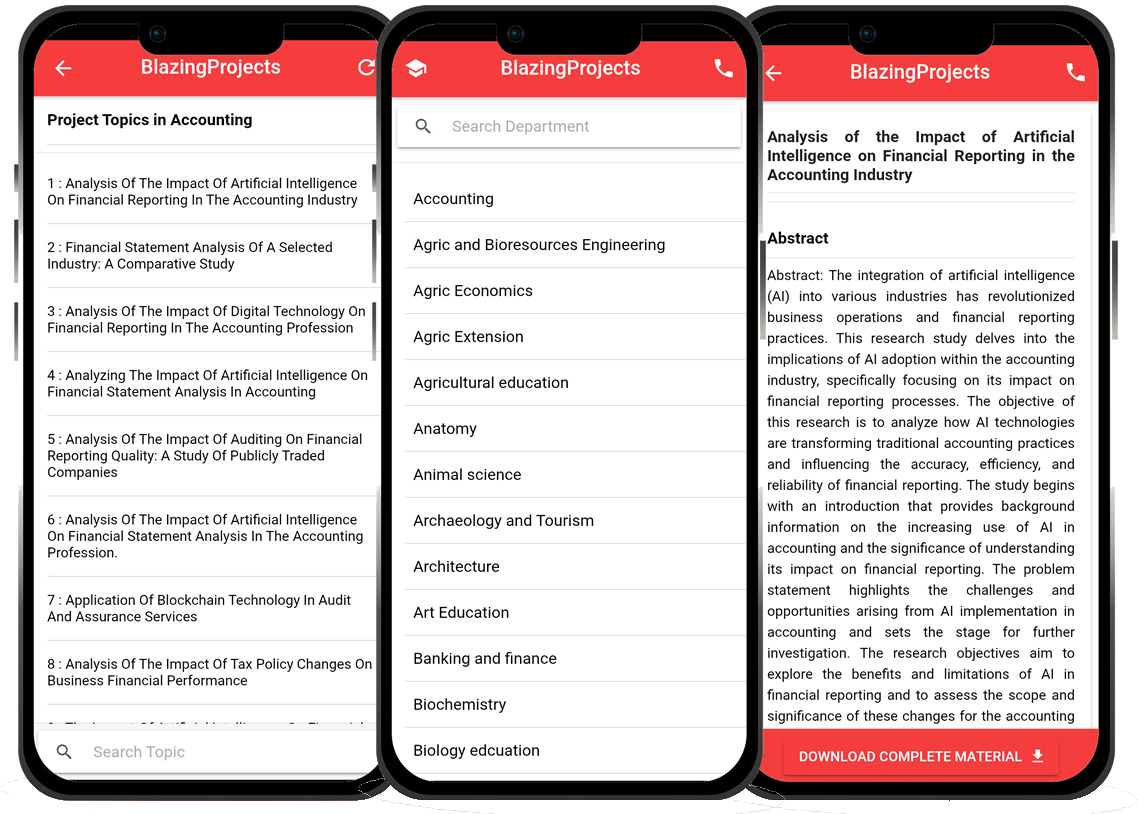
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Applying Machine Learning Techniques to Detect Financial Fraud in Online Transaction...
The project titled "Applying Machine Learning Techniques to Detect Financial Fraud in Online Transactions" aims to address the critical issue of detec...
Anomaly Detection in IoT Networks Using Machine Learning Algorithms...
The project titled "Anomaly Detection in IoT Networks Using Machine Learning Algorithms" focuses on addressing the critical challenge of detecting ano...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project titled "Applying Machine Learning Algorithms for Predicting Stock Market Trends" aims to explore the application of machine learning algor...
Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data...
The project titled "Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data" focuses on utilizing machine learning algorithms...
Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project titled "Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems" focuses on leveraging machine learning techniques ...
Implementation of a Machine Learning Algorithm for Predicting Stock Prices...
The project, "Implementation of a Machine Learning Algorithm for Predicting Stock Prices," aims to leverage the power of machine learning techniques t...
Development of an Intelligent Traffic Management System using Machine Learning Algor...
The project titled "Development of an Intelligent Traffic Management System using Machine Learning Algorithms" aims to revolutionize the traditional t...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
No response received....
Applying Machine Learning for Intrusion Detection in IoT Networks...
The project titled "Applying Machine Learning for Intrusion Detection in IoT Networks" aims to address the increasing cybersecurity threats targeting ...