Curbing software piracy in development environment using code splitting, obfuscation and fingerprinting techniques
Table Of Contents
Chapter ONE
1.1 Introduction 1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Software Piracy 2.2 History of Code Splitting Techniques
2.3 Evolution of Obfuscation in Software Protection
2.4 Fingerprinting Technologies in Software Development
2.5 Legal and Ethical Implications of Software Piracy
2.6 Impact of Software Piracy on Development Environment
2.7 Current Trends in Anti-Piracy Measures
2.8 Comparative Analysis of Protection Techniques
2.9 Case Studies on Successful Anti-Piracy Strategies
2.10 Future Prospects in Software Protection
Chapter THREE
3.1 Research Design and Methodology 3.2 Selection of Research Approach
3.3 Data Collection Methods
3.4 Sampling Techniques
3.5 Data Analysis Procedures
3.6 Validity and Reliability of Research
3.7 Ethical Considerations in Research
3.8 Limitations of the Research Methodology
Chapter FOUR
4.1 Analysis of Data Collected 4.2 Implementation of Code Splitting Techniques
4.3 Evaluation of Obfuscation Strategies
4.4 Utilization of Fingerprinting Technologies
4.5 Comparison of Results with Research Objectives
4.6 Interpretation of Findings
4.7 Discussion on Implications for Development Environment
4.8 Recommendations for Future Practices
Chapter FIVE
5.1 Summary of Findings 5.2 Conclusion
5.3 Contributions to Knowledge
5.4 Implications for Industry Practices
5.5 Recommendations for Further Research
Thesis Abstract
Software Piracy has become a major problem for businesses and its widespread in many parts of the world leads to financial losses and harm to consumers. These problems caused the deployment of many security techniques to control piracy. A lot of researches have been done on software security techniques but unfortunately protecting software source code in development environment has been a challenge for software companies as software source codes are not yet transformed to unreadable codes. Therefore, software piracy emanating from development environments, mostly by insiders, has been a big problem to tackle because the prevalent software protection techniques were primarily developed for use at production stage. Based on the literature review, no research was found on piracy reduction in development environment. In this research work an architecture has been proposed and implemented based on design obfuscation that enables tracking pirated standalone software at development stage using the hardware and software aspects, online or offline, and tracing vulnerable PCs within a company. Code Splitting, obfuscation and fingerprinting techniques were used to design the proposed architecture. Two examination results processing software ExamsLOGIC 2.0 and ELogicPLUS were used to test the proposed architecture for existing and new applications respectively. The result was compared with the result of the reviewed work and found to be improved. For both the two applications, it was found that the proposed architecture is feasible and effective
Thesis Overview
Software Piracy is the unauthorized use, distribution or copying of software illegally. It has become a major problem for businesses and it’s widespread in many parts of the world leads to financial losses and harm to consumers (Rouse, 2005). The Business Software Alliance (BSA) and the Software Publishers Association (SPA) are organizations meant for reducing piracy worldwide. The Business Software Alliance (BSA) is the leading advocate for the global software industry before governments and in the international marketplace. It is an association of nearly 100 world-class companies that invest billions of dollars annually to create software solutions that spark the economy and improve modern life (BSA, 2011) . These organizations estimated that there are two-third illegal copies of software available for every legal copy of software sold and had piracy rates of 62 percent or higher (BSA, 2011). The 2010 BSA/IDC study demonstrates that even a modest reduction in software theft would have significant multiplier effects on the economic contribution of the packaged software industry. This makes software piracy a major problem for the software industries and to the world economy in general.
Software industries always strongly depend on copyrights and other Intellectual Property (IP) to drive innovation and ensure a return on investment in R&D. Hence, protecting their products from being pirated is one of the major tasks they consider in order to keep the company up and running. With the improvement in technology over decades, software vulnerabilities such as Reverse Engineering increase at almost the same pace with technology. For almost every software protection technique there is an equivalent hacking technique for it.
In the case of packaged software, it is common to find counterfeit copies of CDs incorporating the software programs, as well as related packaging, manuals, license agreements, labels, registration cards and security features. Counterfeiting is a serious problem for the software industry, as advances in technology have enabled a growing number and variety of commercial enterprises to manufacture and distribute counterfeit software on a massive scale. This is because the risks of being caught are relatively low and penalties are far less than for engaging in other illegal activities (BSA, 2011).
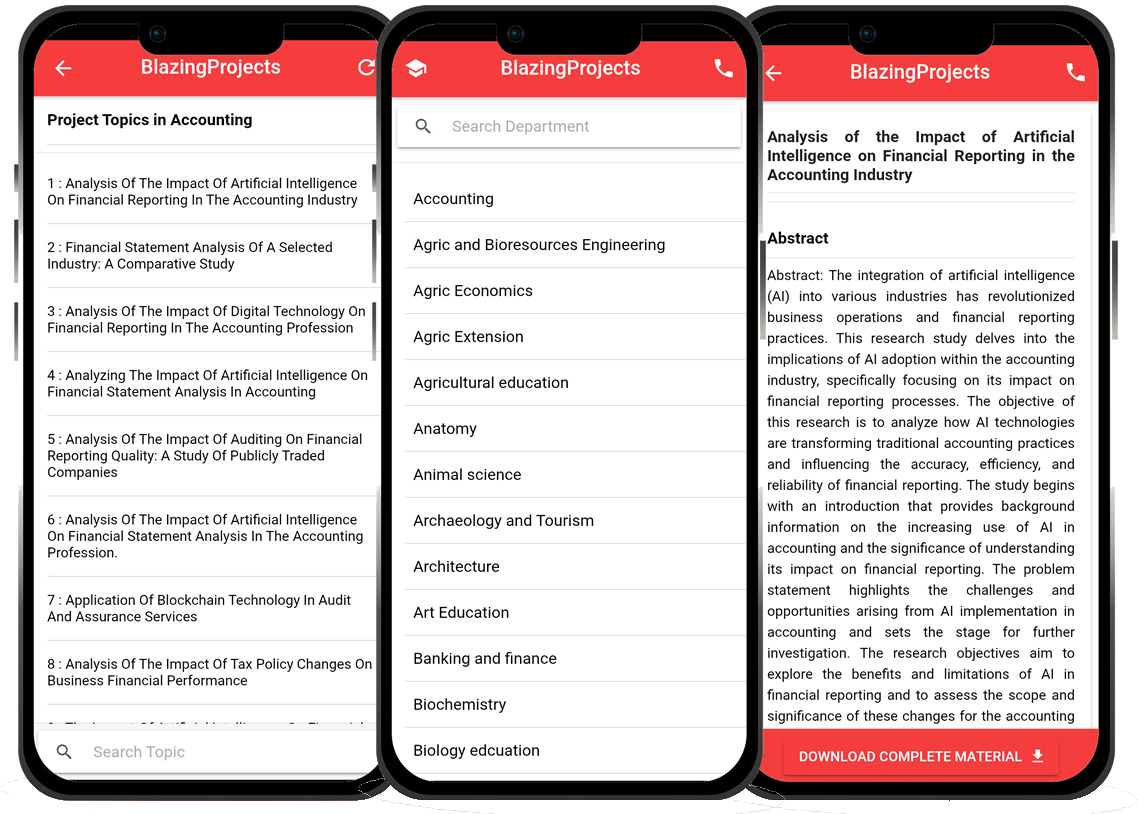
Blazingprojects Mobile App
📚 Over 50,000 Research Thesis
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Thesis-to-Journal Publication
🎓 Undergraduate/Postgraduate Thesis
📥 Instant Whatsapp/Email Delivery
Related Research
Applying Machine Learning Techniques to Detect Financial Fraud in Online Transaction...
The project titled "Applying Machine Learning Techniques to Detect Financial Fraud in Online Transactions" aims to address the critical issue of detec...
Anomaly Detection in IoT Networks Using Machine Learning Algorithms...
The project titled "Anomaly Detection in IoT Networks Using Machine Learning Algorithms" focuses on addressing the critical challenge of detecting ano...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project titled "Applying Machine Learning Algorithms for Predicting Stock Market Trends" aims to explore the application of machine learning algor...
Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data...
The project titled "Applying Machine Learning Algorithms for Sentiment Analysis in Social Media Data" focuses on utilizing machine learning algorithms...
Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project titled "Applying Machine Learning for Predictive Maintenance in Industrial IoT Systems" focuses on leveraging machine learning techniques ...
Implementation of a Machine Learning Algorithm for Predicting Stock Prices...
The project, "Implementation of a Machine Learning Algorithm for Predicting Stock Prices," aims to leverage the power of machine learning techniques t...
Development of an Intelligent Traffic Management System using Machine Learning Algor...
The project titled "Development of an Intelligent Traffic Management System using Machine Learning Algorithms" aims to revolutionize the traditional t...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
No response received....
Applying Machine Learning for Intrusion Detection in IoT Networks...
The project titled "Applying Machine Learning for Intrusion Detection in IoT Networks" aims to address the increasing cybersecurity threats targeting ...