File encryption and hash system using advanced encryption system
Table Of Contents
Chapter ONE
1.1 Introduction1.2 Background of Study
1.3 Problem Statement
1.4 Objective of Study
1.5 Limitation of Study
1.6 Scope of Study
1.7 Significance of Study
1.8 Structure of the Research
1.9 Definition of Terms
Chapter TWO
2.1 Overview of Encryption Systems2.2 Historical Development of Encryption
2.3 Types of Encryption Algorithms
2.4 Applications of Encryption Systems
2.5 Importance of Data Security
2.6 Encryption Standards and Protocols
2.7 Challenges in Encryption Systems
2.8 Encryption Key Management
2.9 Encryption in Communication Systems
2.10 Emerging Trends in Encryption Technology
Chapter THREE
3.1 Research Methodology Overview3.2 Research Design
3.3 Data Collection Methods
3.4 Sampling Techniques
3.5 Data Analysis Procedures
3.6 Research Ethics
3.7 Validity and Reliability
3.8 Research Limitations
Chapter FOUR
4.1 Data Analysis and Interpretation4.2 Encryption System Performance Evaluation
4.3 Comparison of Encryption Algorithms
4.4 Data Security Measures
4.5 Impact of Encryption on Data Privacy
4.6 Encryption Key Management Strategies
4.7 Discussion on Encryption Challenges
4.8 Recommendations for Encryption Implementation
Chapter FIVE
5.1 Summary of Findings5.2 Conclusions
5.3 Implications of the Study
5.4 Contributions to Knowledge
5.5 Recommendations for Future Research
5.6 Conclusion and Final Remarks
Project Abstract
AbstractFile encryption is a crucial aspect of data security, especially in the digital age where cyber threats are prevalent. This research project focuses on developing a file encryption and hash system using an advanced encryption system to enhance data security measures. The system aims to provide robust protection for sensitive files by encrypting them with sophisticated encryption algorithms. The project involves the implementation of advanced encryption standards to ensure the confidentiality and integrity of the encrypted files. Additionally, a hash system is integrated into the encryption process to verify the authenticity and integrity of the files. The hash system generates unique hash values for each file, which can be used to detect any unauthorized modifications to the encrypted files. The encryption system utilizes a combination of symmetric and asymmetric encryption techniques to secure the files effectively. Symmetric encryption is used for encrypting the files, while asymmetric encryption is employed for securely sharing the encryption keys between authorized users. This dual-layer encryption approach enhances the overall security of the system. Furthermore, the research project explores the use of key management techniques to securely store and manage encryption keys. Proper key management is essential for maintaining the security of the encrypted files and preventing unauthorized access. The system incorporates key generation, storage, distribution, and revocation mechanisms to ensure the confidentiality of the encryption keys. In addition to encryption and hash functions, the system includes features such as access control mechanisms and audit trails to monitor and control file access. Access control mechanisms restrict file access to authorized users based on predefined permissions, while audit trails record all file access activities for security monitoring purposes. Overall, the file encryption and hash system developed in this research project offer a comprehensive approach to enhancing data security through advanced encryption techniques. By combining encryption, hash functions, key management, access control, and audit trails, the system provides a robust solution for protecting sensitive files from unauthorized access and tampering. The research outcomes contribute to the advancement of data security practices and can be applied in various industries to safeguard confidential information.
Project Overview
1.0. Introduction
Due to increasing use of computers, security of digital information is most important issue. An Intruder is an unwanted person who reads and changes the information while transmission occurs. This activity of intruder is called intrusion attack. To avoid such attack data may be encrypted to some formats that is unreadable by an unauthorized person. Advanced Encrption System is mainly an advance version of Data Encryption Standard. Efforts towards developing Advanced Encrption System was started by National Institute from January 1997.
Using Cryptography is essential so that the medium of file communication can secured, as its main objective is implementing the public and private key(s) with hash functions or authentication codes or digital signatures. However it provides confidentiality by itself because mostly, the concerning person knows that the message is hidden in what kind of medium (Ali et al., 2011).
1.1 Background of the Study
The most powerful and common approach to countering the threats to network / information security is using Encryption (Ayoub, 1994). Encryption is based on number of substitutions, transpositions we perform on the plaintext, converted plain text is treated as cipher text and a process of converting is called Cryptography (William, 2005). Even though encryption is very powerful among these two, the cryptanalysts are very intelligent and they were working day and night to break the ciphers. To make a stronger cipher it is recommended that to use: More stronger and complicated encryption algorithms with more number of rounds, Keys with more number of bits (Longer keys), secure transmission of keys (Ravindra, 2010).
Information transmission through internet may include sensitive personal data which may be intercepted. Also, there are many applications on the internet and many web sites require the users to fill forms that include sensitive personal information such as telephone numbers, addresses, and credit card information. So, the users may need private and secure communications for many reasons such as protect their confidential information from hackers during it passed over an open channel, so the confidentiality and data integrity are required to protect against unauthorized access and use. Cryptography is a common methods used in today’s world to secure communications of files of different types (Petitcolas, 1999).
Cryptography is meant to enable the confidentiality of communication through an insecure channel that is protected against unauthorized parties, by preventing unauthorized alteration of use (Vaudenay, 2005).
Cryptography is the science of using mathematics to encrypt and decrypt data to keep messages secured by transforming intelligible data form (plaintext) into unintelligible form (ciphertext). The term cryptography has come from the Greek word “kryptós” standing for “hidden” and “gràphin” standing for “writing”. Thus, the proper meaning of cryptography is “hidden writing”. Any cryptosystem consists of plaintext, encryption algorithm, decryption algorithm, Cipher text, and Key. Plaintext is message or data which are in their normal, readable (not encrypted) form. Encryption is the process of converting plaintext to cipher text by using key. Cipher text results from encryption by applying the encryption key on the plaintext. Decryption is the process of retrieving the plaintext back from the cipher text. The Key is used info to control the cryptosystem (cipher system), and it is known by the sender and receiver only (Schneier, 1996). While cryptography is very powerful for securing data; the cryptanalysts could success to break the ciphers by analyzing the contents of cipher text to get back the plaintext (Babu, 2010).
Advanced Encrption System is a symmetric key encryption algorithm, and NIST made a worldwide public call for the algorithm to succeed Data Encryption System. Initially 15 algorithms were selected. After detail analysis they were reduced down to 5 algorithms namely MARS, RC6, Rijndael, Serpent and Twofish. All these algorithms were iterated block ciphers. The all five finalists were determined to be qualified as the algorithm for Advanced Encryption System. After complete analysis Rijndael is selected as the algorithm for Advanced Encryption System (William, 2006).
Rijndael Algorithm can be seen to possess the following features: High security, mathematical soundness, resistance to all known attacks, high encryption speed, worldwide royalty free use, suitability across wide range of hardware and software.
The Rijndael algorithm is a symmetric block cipher that can process data blocks
of 128 bits through the use of cipher keys with lengths of 128, 192, and 256 bits. The Rijndael algorithm was also designed to handle additional block sizes and key lengths.
1.2 Statement of the Problem
Without adequately being able to protect files of varying types and sizes, a lot of harm can be done to individuals and cooperate bodies, who constantly send informations that can be described as being sensitive. With this study, a refined approach will be adopted, which will go a long way in curbing information hijacking and theft.
1.3 Aim and Objectives of the Study
The aim of this study is basically to develop a File Encryption application using Hash System alongside Advanced Encryption System, to better protect sensitive files.
The specific objectives are:
To elaborate on the process of cryptography.
To elaborate on types of Hash systems.
To elaborate on the types of encryptions available.
To elaborate on the importance of Advanced Encryption system
1.4 Scope and Limitation
This research work titled File Encryption And Hash System Using Advanced Encryption System focuses on the use of hash system in conjunction with advanced encryption system, for file encryption in other to protect information’s. This study is limited to digital files protection.
1.5 Significance of the Study
To help digital device users to better protect their sensitive files.
To help protect top government and companies files from.
To elaborate on the ways files can be protected using advanced encryption
1.6 Definition of Terms
Encryption: The process of encoding informations in a form that only the authorized parties can understand.
Cryptography: This is the practice and study of techniques for secure communication.
Hash system: This enables the conversion of a digital document, before it can be encrypted to enhance its security.
Digital File: A collection of data stored in a particular format, on computer devices.
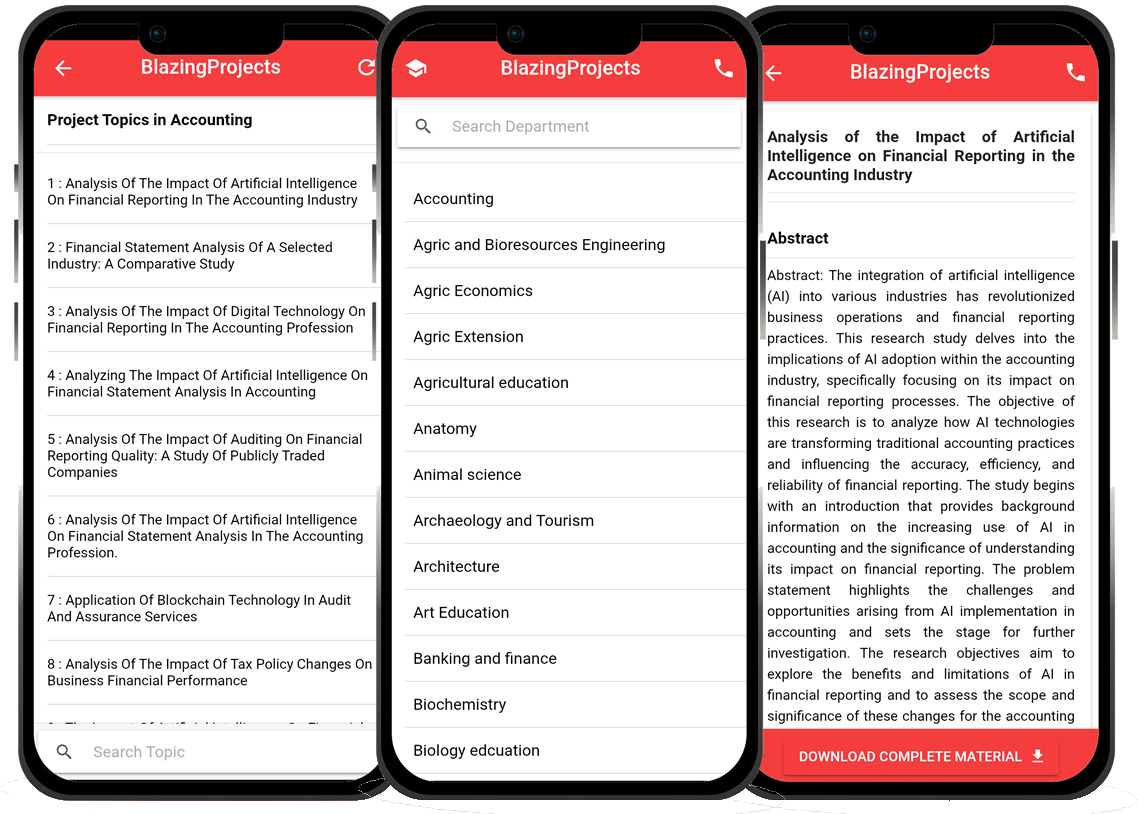
Blazingprojects Mobile App
📚 Over 50,000 Project Materials
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Software coding and Machine construction
🎓 Postgraduate/Undergraduate Research works
📥 Instant Whatsapp/Email Delivery
Related Research
The Impact of Social Media Influencers on Consumer Behavior in the Fashion Industry...
The fashion industry has experienced significant transformations in recent years due to the rise of social media influencers. These online personalities have be...
Exploring the Impact of Social Media Influencers on Consumer Behavior in the Fashion...
The research project titled "Exploring the Impact of Social Media Influencers on Consumer Behavior in the Fashion Industry" aims to investigate the in...
The Impact of Social Media Influencers on Consumer Behavior: A Study of Millennials...
The research project titled "The Impact of Social Media Influencers on Consumer Behavior: A Study of Millennials" aims to investigate the influence of...
Analyzing the Impact of Social Media Influencers on Consumer Behavior in the Beauty ...
The project titled "Analyzing the Impact of Social Media Influencers on Consumer Behavior in the Beauty Industry" aims to investigate the significant ...
The Impact of Social Media Influencers on Consumer Behavior in the Beauty Industry...
The beauty industry has undergone a significant transformation in recent years with the advent and widespread adoption of social media platforms. Social media i...
The Impact of Social Media Influencers on Consumer Behavior: A Case Study of Beauty ...
The project topic, "The Impact of Social Media Influencers on Consumer Behavior: A Case Study of Beauty Product Advertising," delves into the dynamic ...
The Impact of Social Media Influencers on Consumer Behavior in Mass Communication In...
The Impact of Social Media Influencers on Consumer Behavior in the Mass Communication Industry In recent years, the rise of social media platforms has revoluti...
An analysis of the impact of social media influencers on consumer behavior in the fa...
The research project focuses on exploring and analyzing the significant influence that social media influencers exert on consumer behavior within the fashion in...
Exploring the Impact of Social Media Influencers on Consumer Behavior in the Fashion...
The project topic, "Exploring the Impact of Social Media Influencers on Consumer Behavior in the Fashion Industry," delves into the dynamic relationsh...