Design and implementation of computerised students identity card system
Table Of Contents
Project Abstract
No response received.Project Overview
INTRODUCTION
1.0 Introduction
An identity document is any document which may be used to verify aspects of a person’s personality. If issued in the form of a small, mostly standard-sized card, it is usually called an identity card (IC). Countries which do not have formal identity documents may require informal documents.
In the absence of formal identity document, driving licenses can be used in many countries as a method of proof of identity, although some countries do not accept driving licenses for identification, often because in those countries they do not expire as documents and can be old easily forged. Most countries accepts passports as a form of identification.
Most countries have the rule that foreign citizens need to have their passport or occasionally a national identity card from their country, available at anytime if they do not have residence permit in the country. A student identification card can only be issued to genuine bonafide students. Card holders can use the card to identify themselves as a student around the campus or outside the campus. The identity card is managed and administered by the (Student Identity Card Association (SICA) of the school.
1.1 Theoretical Background
Today, it is believed that the application of computer technology in any activity would go a long way in making that activity much easier. To the research, this statement remains a theory until proven otherwise by the implementation of a computerized student ID-card processing system. It is also believed that benefits and advantage of using computers outweighs that of manual methods.
This also wants to be proven beyond doubts by the researcher through the implementation of the new system.
1.2 Statement of the Problem
The major problems that gave rise to this research project is faced by Akwa Ibom State Polytechnic and they include late registration of student’s, corrupt students that know diverse ways of producing fake identity cards, corrupt and tactical student’s who have a way of sneaking into the examination hall with fake identity cards.
1.3 Aim and Objectives of the Study
The aim of the study is to design and implement workable computerized system for student’s identity cards.
The objectives of the study are as follows:
1. To establish efficient means of tracking students with fake ID-Card.
2. To reduce examination malpractice in Akwa Ibom State Polytechnic, at least in the area of impersonation
3. To create a reliable database of students in Akwa Ibom State Polytechnic, with unique features like passport photographs and registration numbers.
4. For research purpose (project writing defense).
1.4 Significance of the Study
This research work would be unnecessary if it has no significance to humanity.
Firstly, the newly designed system would make other-higher institutions to see the need for creating a computerized student ID-card processing system to use in production of student ID-card.
Secondly, the knowledge that the new system has designed would make students and invigilators contemplating on impersonation and have a change of mind for fear of being caught.
Thirdly, the designed of the system would provide jobs for system analysts and programmers contacted to build the system for other institutions.
Fourthly, student identity card is used to check out books from the library, register to vote on student union matters, and get student discount.
Finally, the research projects would serve as reference material to other scholars interested to further research on the topic.
1.5 Scope of the Study
This research work restricted to implementation of computerized student ID-card processing system; using Akwa Ibom State Polytechnic as a case study. Data used for the study were gathered from this source.
1.6 Organization of the Research
This research work has been arrange in the following order:
Chapter one contains introduction, theoretical background, statement of the problem, aim and objectives of the study, significance of the study, scope of the study, organization of the research and definition of terms (where necessary).
Chapter two focused on the relevant literature review, highlighting basic concept.
Chapter three is concerned with the system design which emphasis on system design and flowcharting. It also expands the development of the new information system that would facilitate tracking of fake ID-cards.
Chapter four is the system implementation which gives the direction of system and analysis of modules.
Chapter five summarizes and concludes the research work offering some useful recommendations.
1.7 Definition of Terms
In order to do away with ambiguity, some terms and keywords in the context of this research are hereby defined.
Identity Card: It is a proof of the holder’s identity that includes a photograph.
Impersonation: The act of pretending to be avoid candidate in order to write examination for someone else using that person identity card.
Verification: Is the evidence that proves that something is true or current.
Photograph: It is an image appeared on the identity card owner.
Malpractice: Is a careless, wrong, or illegal practices that is not ethical in a particular field like academics.
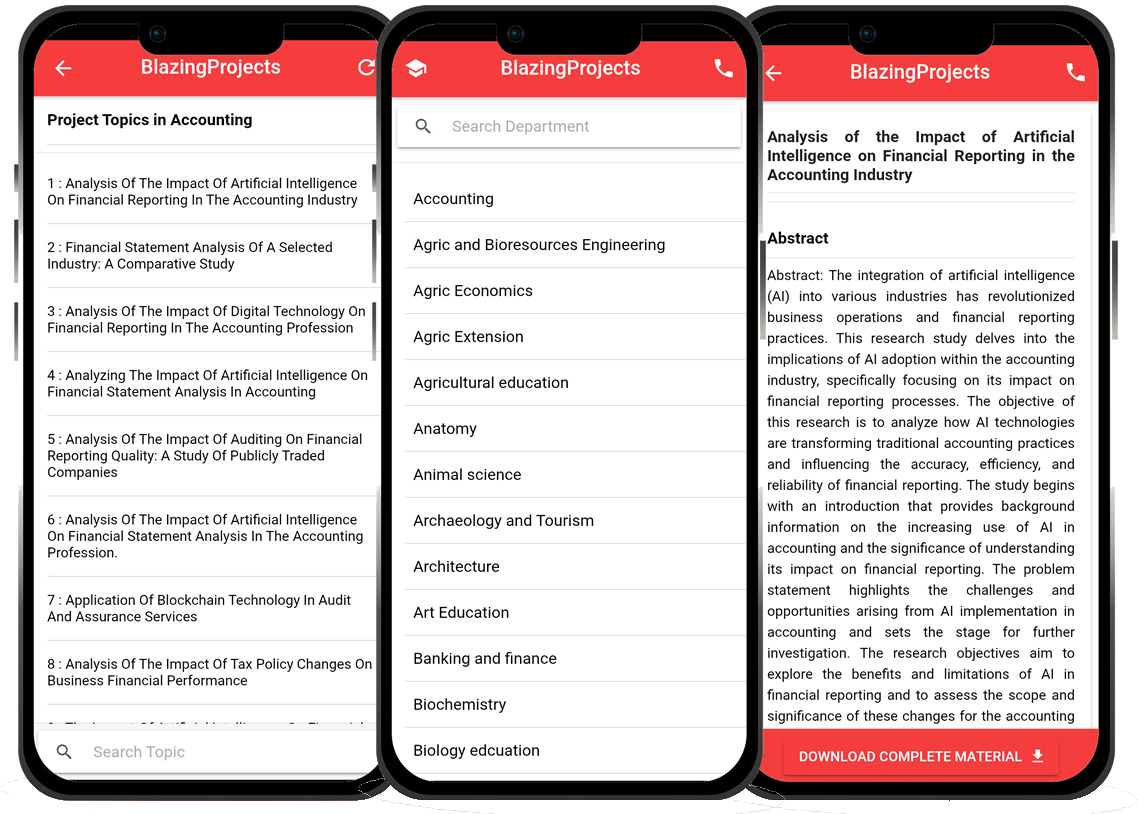
Blazingprojects Mobile App
📚 Over 50,000 Project Materials
📱 100% Offline: No internet needed
📝 Over 98 Departments
🔍 Software coding and Machine construction
🎓 Postgraduate/Undergraduate Research works
📥 Instant Whatsapp/Email Delivery
Related Research
Predicting Disease Outbreaks Using Machine Learning and Data Analysis...
The project topic, "Predicting Disease Outbreaks Using Machine Learning and Data Analysis," focuses on utilizing advanced computational techniques to ...
Implementation of a Real-Time Facial Recognition System using Deep Learning Techniqu...
The project on "Implementation of a Real-Time Facial Recognition System using Deep Learning Techniques" aims to develop a sophisticated system that ca...
Applying Machine Learning for Network Intrusion Detection...
The project topic "Applying Machine Learning for Network Intrusion Detection" focuses on utilizing machine learning algorithms to enhance the detectio...
Analyzing and Improving Machine Learning Model Performance Using Explainable AI Tech...
The project topic "Analyzing and Improving Machine Learning Model Performance Using Explainable AI Techniques" focuses on enhancing the effectiveness ...
Applying Machine Learning Algorithms for Predicting Stock Market Trends...
The project topic "Applying Machine Learning Algorithms for Predicting Stock Market Trends" revolves around the application of cutting-edge machine le...
Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems...
The project topic, "Application of Machine Learning for Predictive Maintenance in Industrial IoT Systems," focuses on the integration of machine learn...
Anomaly Detection in Internet of Things (IoT) Networks using Machine Learning Algori...
Anomaly detection in Internet of Things (IoT) networks using machine learning algorithms is a critical research area that aims to enhance the security and effic...
Anomaly Detection in Network Traffic Using Machine Learning Algorithms...
Anomaly detection in network traffic using machine learning algorithms is a crucial aspect of cybersecurity that aims to identify unusual patterns or behaviors ...
Predictive maintenance using machine learning algorithms...
Predictive maintenance is a proactive maintenance strategy that aims to predict equipment failures before they occur, thereby reducing downtime and maintenance ...